When you visit a website running over HTTPS a series of steps are performed between the browser and the web server to ensure the certificate and SSL/TLS connection is valid.
Some of these include the TLS handshake, the certificate being checked against the certificate authority, and decryption of the certificate.
What Is the ERR_SSL_VERSION_OR_CIPHER_MISMATCH Error?
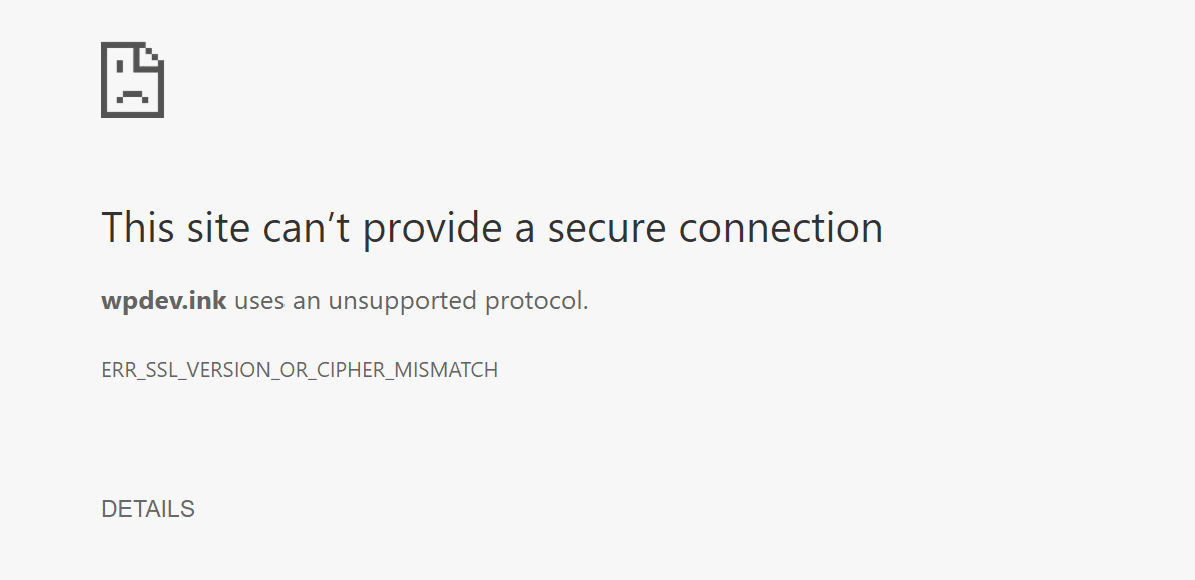
If for some reason the browser doesn’t like what it sees, such as a misconfiguration or unsupported version, your browser might display the following error: “ERR_SSL_VERSION_OR_CIPHER_MISMATCH” which prevents you from accessing the site.
Check out a few recommendations on how to fix this error.
What Causes the ERR_SSL_VERSION_OR_CIPHER_MISMATCH Error?
The ERR_SSL_VERSION_OR_CIPHER_MISMATCH error typically happens on older operating systems or browsers.
But that is not always the case. In fact, we just recently encountered a user having this issue on their WordPress site who was migrating to Kinsta from another host. We were, of course, running the latest version of Chrome, so the issue was with their SSL certificate. Chrome is actually protecting you by not letting you load it.
You might also see a variation of the error, such as:
- Error 113 (net::err_ssl_version_or_cipher_mismatch): unknown error
- The client and server don’t support a common SSL protocol version or cipher suite
How to Fix the ERR_SSL_VERSION_OR_CIPHER_MISMATCH Error?
Check out the main solutions below and what you can do about it.
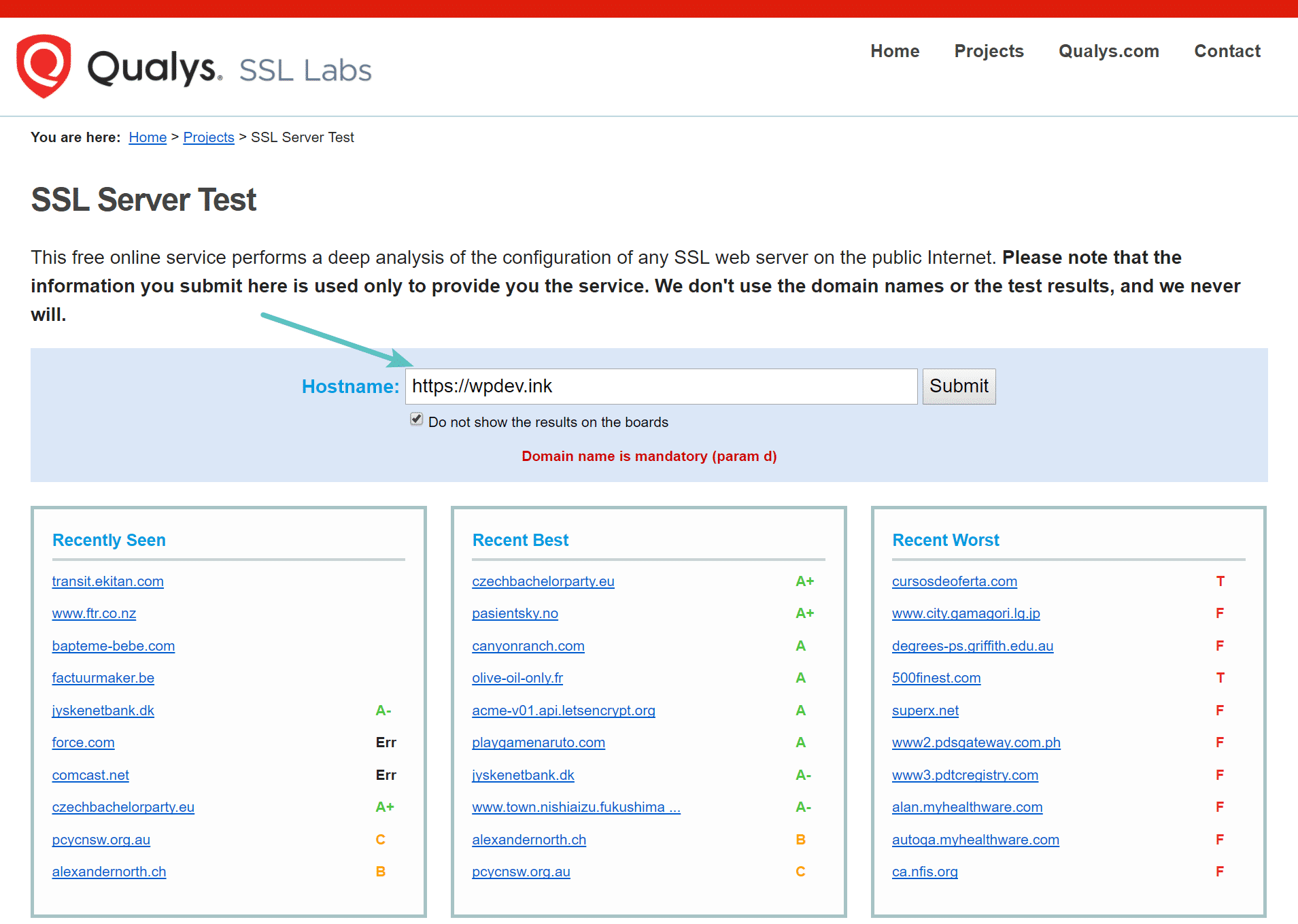
Check Your SSL Certificate
If you see this error, the first and easiest place to start is to perform an SSL check on the certificate that is installed on the site. We recommend using the free SSL check tool from Qualys SSL Labs. It is very reliable and we use it for all Kinsta clients when verifying certificates. Simply input your domain into the Hostname field and click on “Submit.”
You can also select the option to hide public results if you prefer. It could take a minute or two to scan your site’s SSL/TLS configuration on your web server.
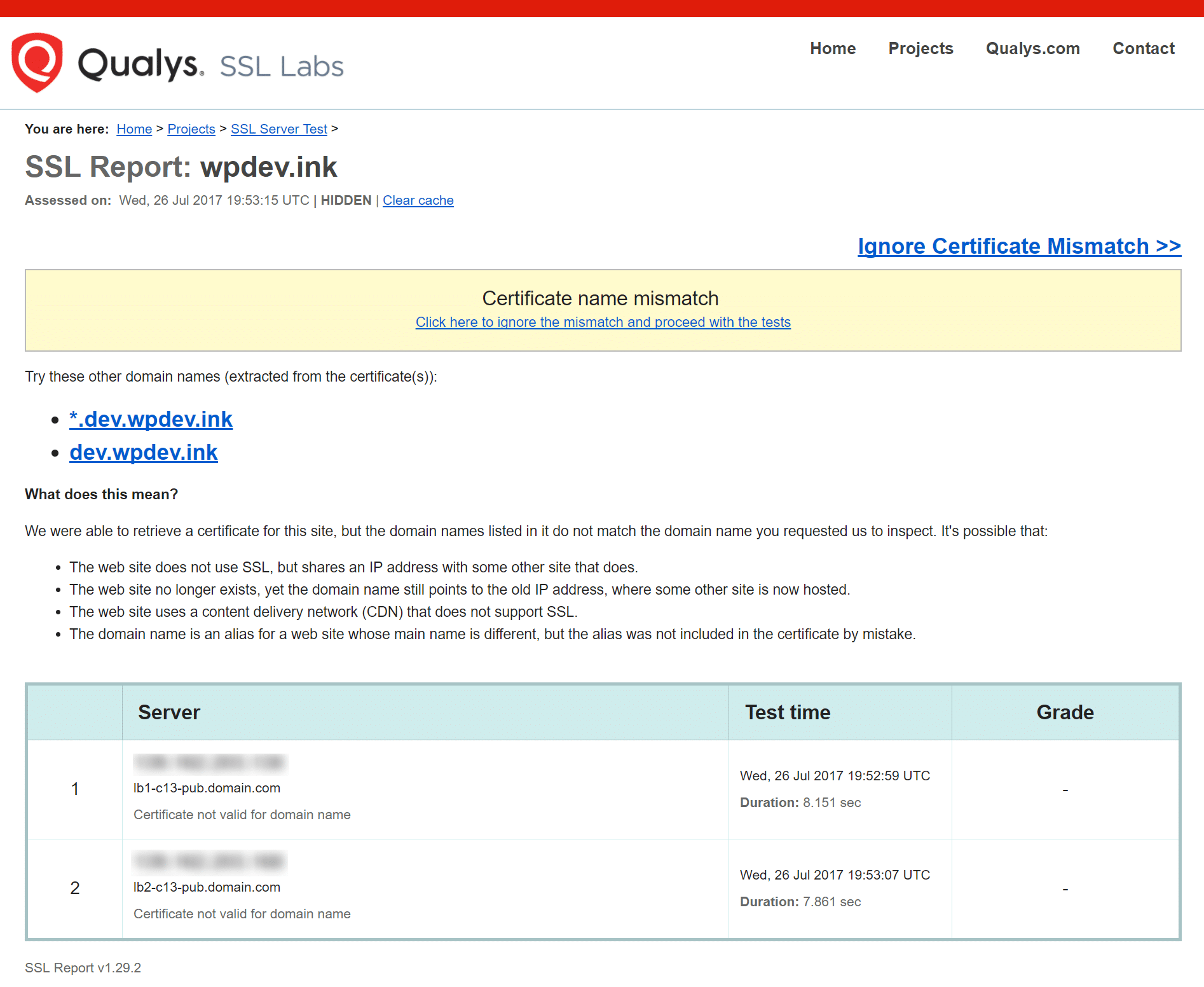
Check for Certificate Name Mismatch
In this particular instance, the customer migrating to Kinsta had a certificate name mismatch which was throwing up the ERR_SSL_VERSION_OR_CIPHER_MISMATCH error. As you can see from the SSL Labs test below, this is pretty quick and easy to diagnose. As SSL Labs states, a mismatch can be a number of things such as:
- The site does not use SSL, but shares an IP address with some other site that does.
- The site no longer exists, yet the domain still points to the old IP address, where some other site is now hosted.
- The site uses a content delivery network (CDN) that doesn’t support SSL.
- The domain name alias is for a website whose name is different, but the alias was not included in the certificate.
Another easy way to check the current domain name issue on the certificate is to open up Chrome DevTools on the site. Right-click anywhere on the website and click on “Inspect.” Then click on the security tab and click on “View certificate.” The issued domain will show in the certificate information. If this doesn’t match the current site you’re on, this is a problem.
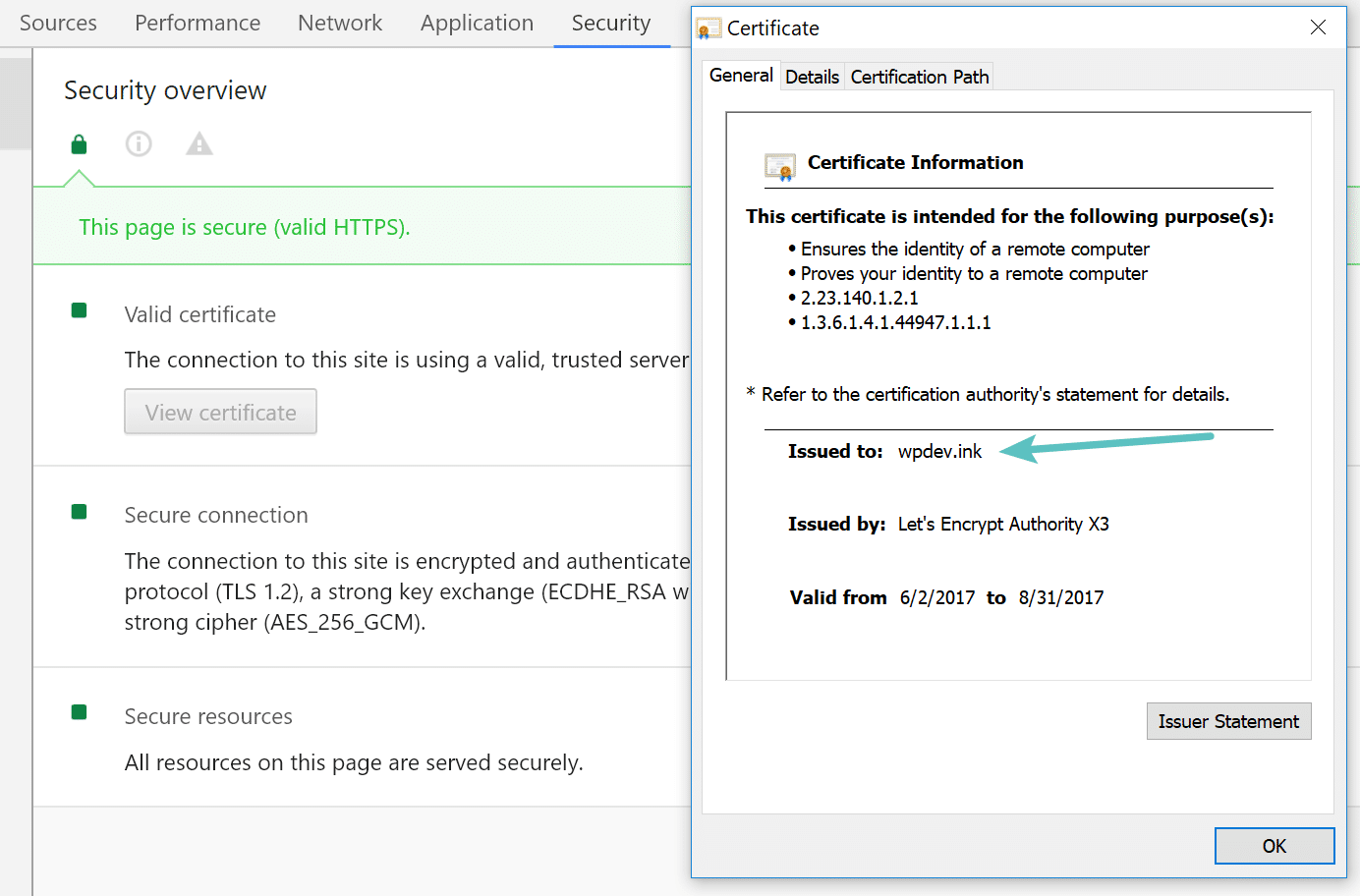
Remember though, there are wildcard certificates and other variations, but for a typical site, it should match exactly. However, in our case, the ERR_SSL_VERSION_OR_CIPHER_MISMATCH error actually prevented us from being able to check it in Chrome DevTools. That is where a tool like SSL Labs can come in handy.
Check for Old TLS version
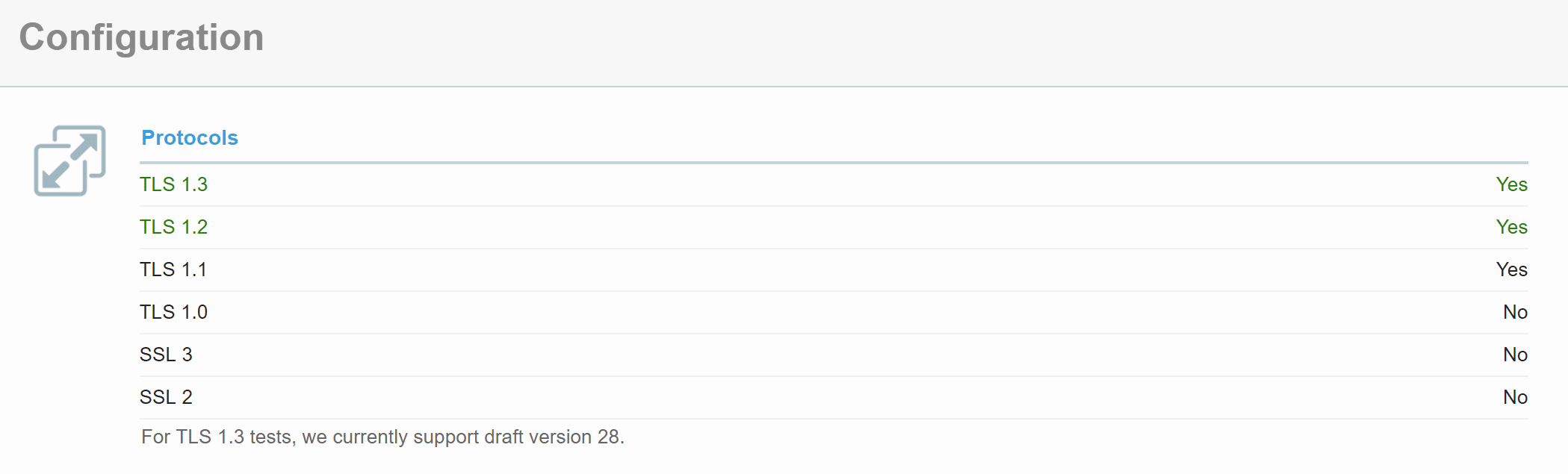
Another possible reason is that the TLS version running on the web server is old. Ideally, it should be running at least TLS 1.2 (better yet, TLS 1.3). If you are a Kinsta customer you never have to worry about this as we always upgrade our servers to the latest and greatest supported versions. Kinsta supports TLS 1.3 on all of our servers and our Kinsta CDN. Cloudflare also enables TLS 1.3 by default.
(Suggested reading: if you’re using legacy TLS versions, you might want to fix ERR_SSL_OBSOLETE_VERSION Notifications in Chrome).
This is something the SSL Labs tool can also help with. Under configuration, it will show you the current version of TLS running on the server with that certificate. If it is old, reach out to your host and ask them to update their TLS version.
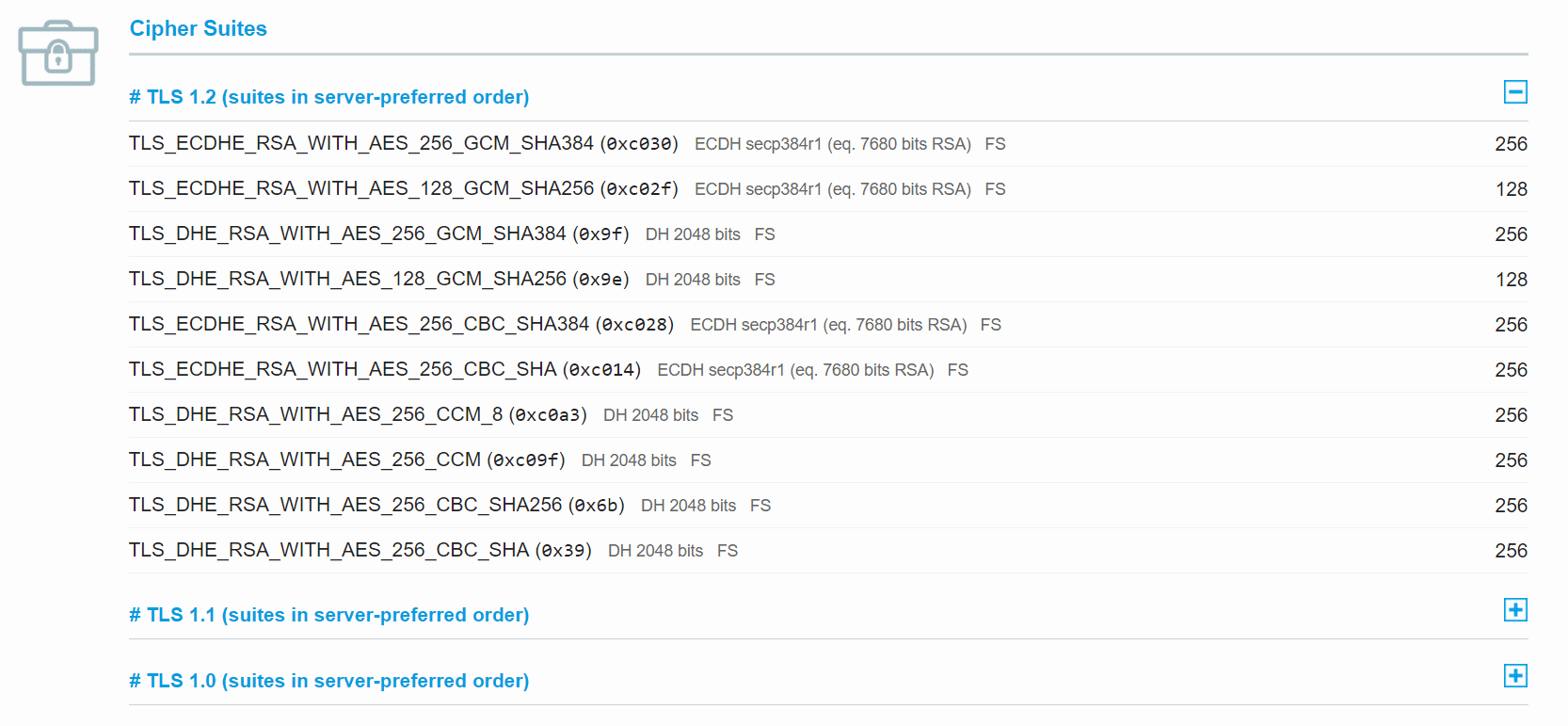
Check RC4 Cipher Suite
Another reason according to Google’s documentation for ERR_SSL_VERSION_OR_CIPHER_MISMATCH is that the RC4 cipher suite was removed in Chrome version 48. This is not very common, but it could happen in say larger enterprise deployments that require RC4. Why? Because everything usually takes longer to upgrade and update in bigger and more complex configurations.
Security researchers, Google, and Microsoft recommend that RC4 be disabled. So you should make sure the server configuration is enabled with a different cipher suite. You can view the current cipher suite in the SSL Labs tool (as seen below).
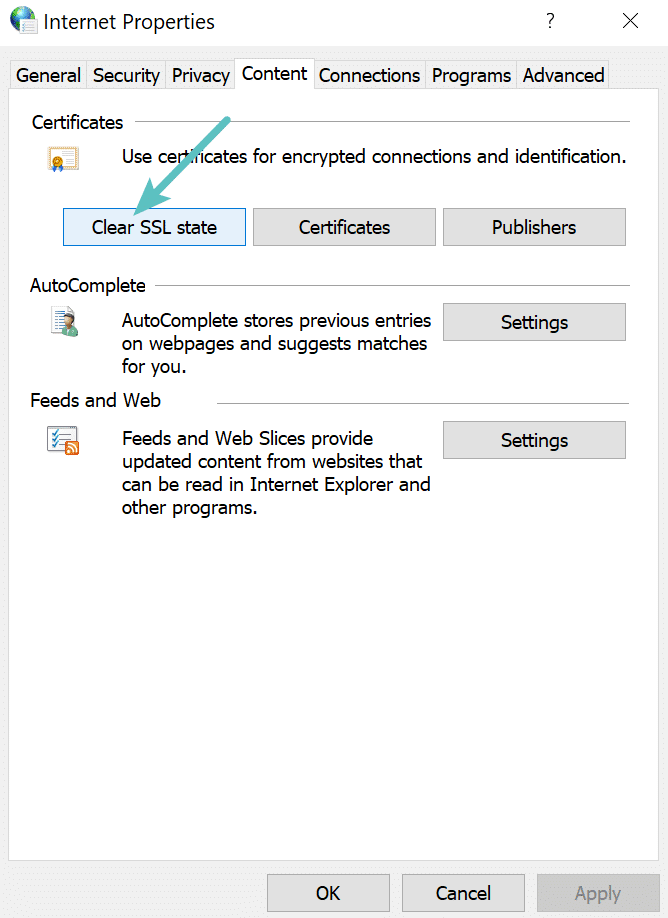
Clear the SSL State In Chrome
Another thing to try is clearing the SSL state in Chrome. Just like clearing your browser’s cache this can sometimes help if things get out of sync. To clear the SSL state in Chrome on Windows, follow these steps:
- Click the Google Chrome – Settings icon (Settings) icon, and then click Settings.
- Click Show advanced settings.
- Under Network, click Change proxy settings. The Internet Properties dialog box appears.
- Click the Content tab.
- Click “Clear SSL state”, and then click OK.
- Restart Chrome.
If you are on a Mac, here’s how you can delete an SSL certificate:
- From the Finder, click Go -> Utilities -> KeyChain Access.
- In the left pane, click on System.
- Click on the certificate that you wish to delete.
- In the menu bar, click on Edit -> Delete. You will be prompted for confirmation.
- Provide your password to modify the keychain. This is likely your login password.
- After a brief wait, you should no longer see the certificate in the certificate list.
We’ve taken our knowledge of effective website management at scale, and turned it into an ebook and video course. Click on the link to download The Guide to Managing 60+ WordPress Sites!
Use a New Operating System
Older operating systems fall out of date with newer technologies such as TLS 1.3 and the latest cipher suites as browsers stop supporting them. Specific components in the latest SSL certs will simply stop working. Google Chrome, in fact, pulled the plug on Windows XP back in 2015. We always recommend upgrading to newer operating systems if possible, such as Windows 10 or the latest version of Mac OS X.
Temporary Disable Antivirus
The last thing we recommend trying if you are still seeing the ERR_SSL_VERSION_OR_CIPHER_MISMATCH error is to ensure you don’t have an antivirus program running. Or try temporarily disabling it. Some antivirus programs create a layer between your browser and the web with their own certificates. This can sometimes cause issues.