Ensuring security is set up correctly for your WordPress site is very important, especially when it comes to protecting yourself from hackers. There are numerous different enhancements and best WordPress security practices you can implement to ensure that your site is locked down. If your WordPress site runs over HTTPS, then one of the enhancements we recommend implementing is the HSTS security header, as it can help prevent man-in-the-middle attacks (MitM) and cookie hijacking.
- HSTS (Strict Transport Security)
- How to Add HSTS to Your WordPress Site
- Verify HSTS Header
- HSTS Impact on SEO
What is HSTS (Strict Transport Security)?
HSTS stands for HTTP Strict Transport Security and was specified by the IETF in RFC 6797 back in 2012. It was created as a way to force the browser to use secure connections when a site is running over HTTPS. It is a security header in which you add to your web server and is reflected in the response header as Strict-Transport-Security. HSTS is important because it addresses the following issues:
- Any attempts by visitors to use the unsecured version (HTTP://) of a page on your site will be automatically forwarded to the secure version (HTTPS://).
- Old HTTP bookmarks and people typing the HTTP version of your site are open you up to man-in-the-middle attacks. These are attacks where the attacker alters communication between parties and tricks them into thinking they are still communicating with each other.
- Doesn’t allow for the overriding of the invalid certificate message which really, in turn, protects the visitor.
- Cookie hijacking: This can occur when someone steals a session cookie over an unsecured connection. Cookies can contain all sorts of valuable information such as credit card information, names, addresses, etc.
How to Add HSTS to Your WordPress Site
Technically you are adding HSTS to the web server itself, which is then applied to HTTP requests to your WordPress site. Typically a 301 redirect is added when doing a redirect from HTTP to HTTPS. Google has officially said that you can use both 301 server redirects as well as the HSTS header together.
Although our systems prefer the HTTPS version by default, you can also make this clearer for other search engines by redirecting your HTTP site to your HTTPS version and by implementing the HSTS header on your server. Zineb Ait Bahajji, Google Security Team
There are different types of directives and or levels of security that can be applied to the HSTS header. Below is the most basic one which uses the max-age directive. This defines the time in seconds for which the web server should only deliver through HTTPS.
Enable HSTS in Apache
Add the following code to your virtual hosts file.
Header always set Strict-Transport-Security max-age=31536000Enable HSTS in NGINX
Add the following code to your NGINX config.
add_header Strict-Transport-Security "max-age=31536000";If you’re a Kinsta client and want to add the HSTS header to your WordPress site you can open up a support ticket and we can quickly add it for you. In fact, there are performance benefits from adding the HSTS header. If someone tries to visit your site via HTTP, instead of an HTTP request being made, it’s simply redirected over to the HTTPS version.
Preload HSTS
There is also HSTS preloading. This is basically getting your website and or domain on an approved HSTS list that is actually built into the browser. Google officially compiles this list and it is utilized by Chrome, Firefox, Opera, Safari, IE11, and Edge. Submit your site to the official HSTS preload list.
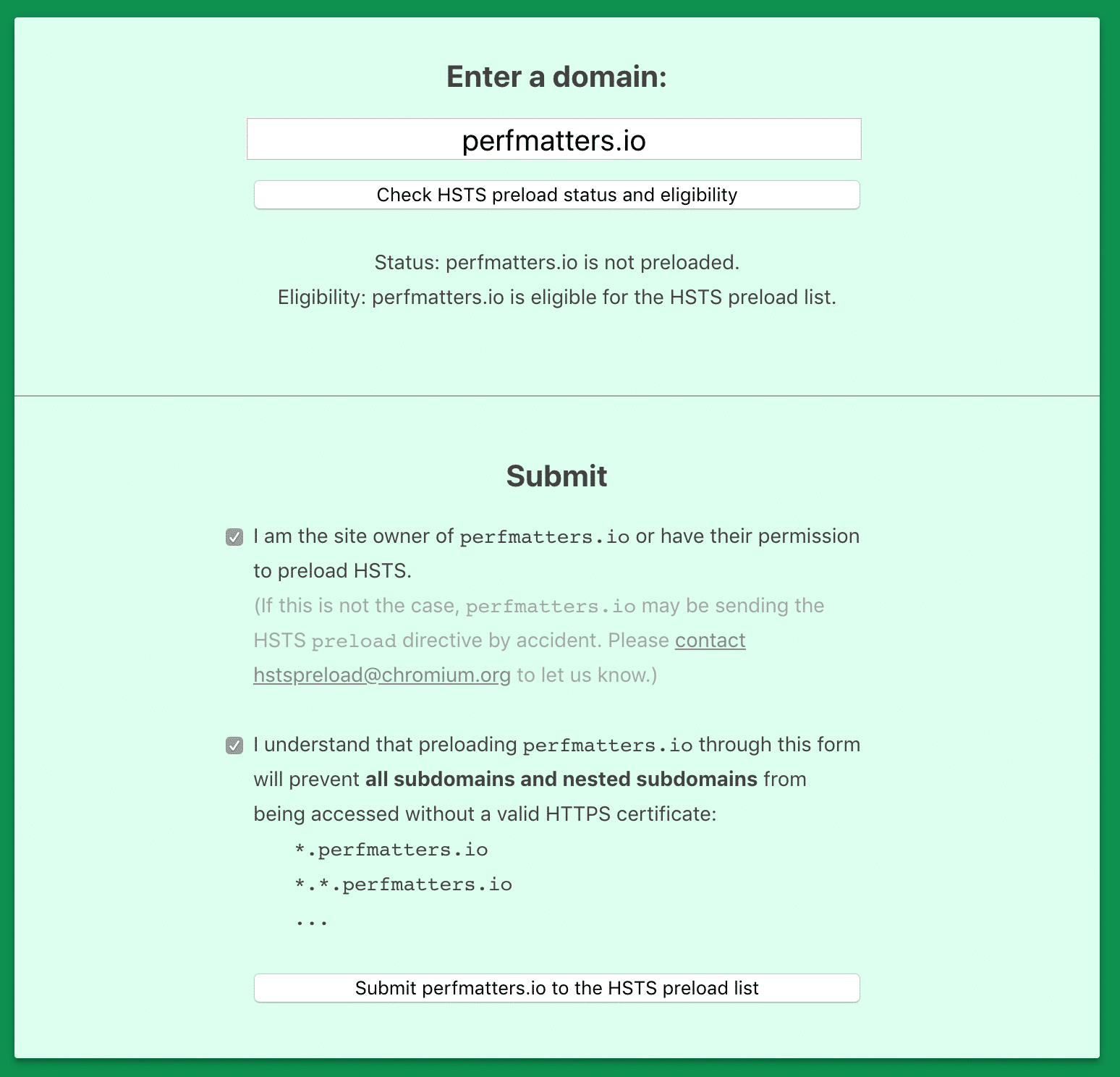
However, you must meet some additional requirements to be eligible.
- The server must have a valid SSL/TLS certificate (TLS vs SSL: what’s the difference?).
- Redirect all traffic to HTTPS.
- Serve HSTS on the base domain.
- Serve all subdomains over HTTPS, specifically including the www subdomain if it exists.
- Expiry must be at least 1 year (31536000 seconds)
- The includeSubdomains token directive must be specified
- The preload token directive must be specified.
To do this it requires adding the additional subdomains and preload directives to your HSTS header. Below is an example of the updated HSTS header.
add_header Strict-Transport-Security "max-age=31536000; includeSubDomains; preload";Fair warning: It can be a difficult and time-consuming process to get your domain removed from the preload list, so ensure you are going to be using HTTPS for the long haul.
Verify HSTS Header
There are a couple easy ways to check if the HSTS is working on your WordPress site. You can launch Google Chrome Devtools, click into the “Network” tab and look at the headers tab. As you can see below on our Kinsta website the HSTS value: “strict-transport-security: max-age=31536000” is being applied.
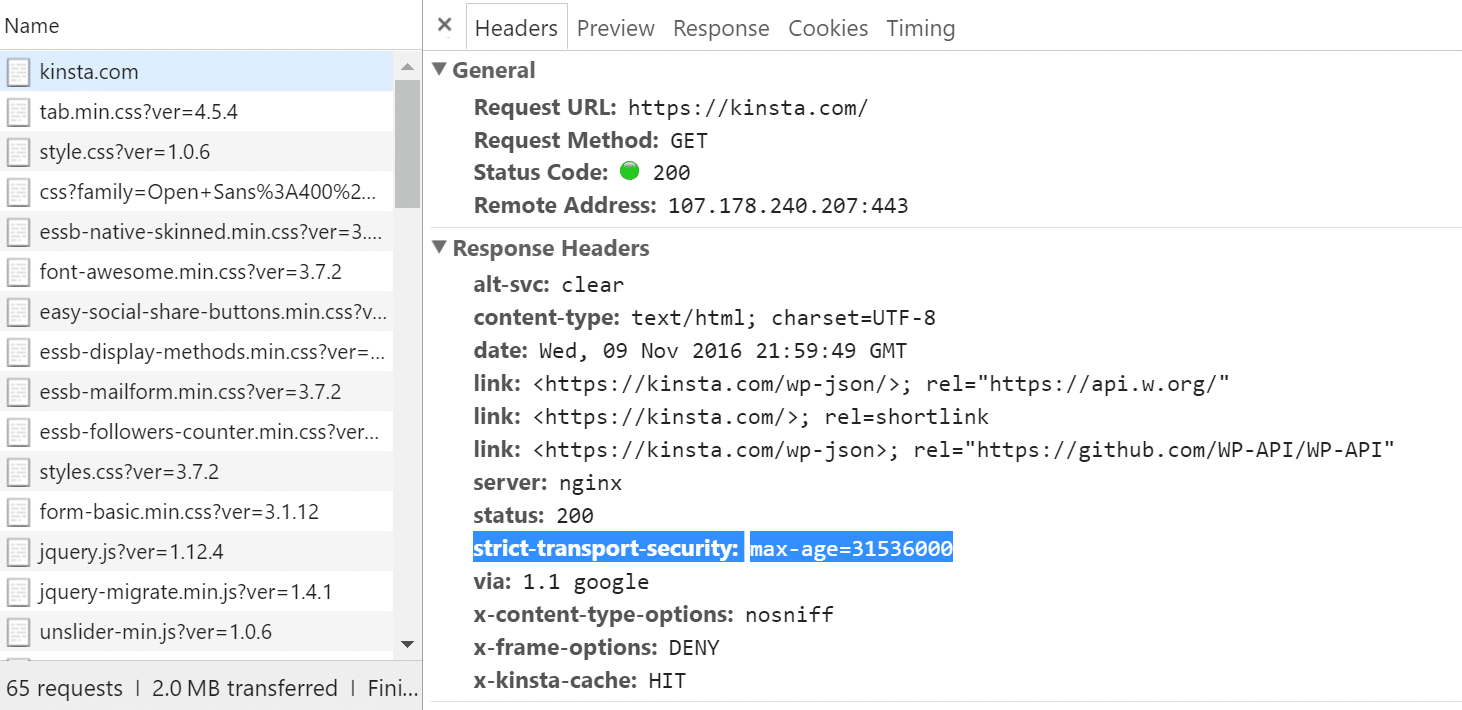
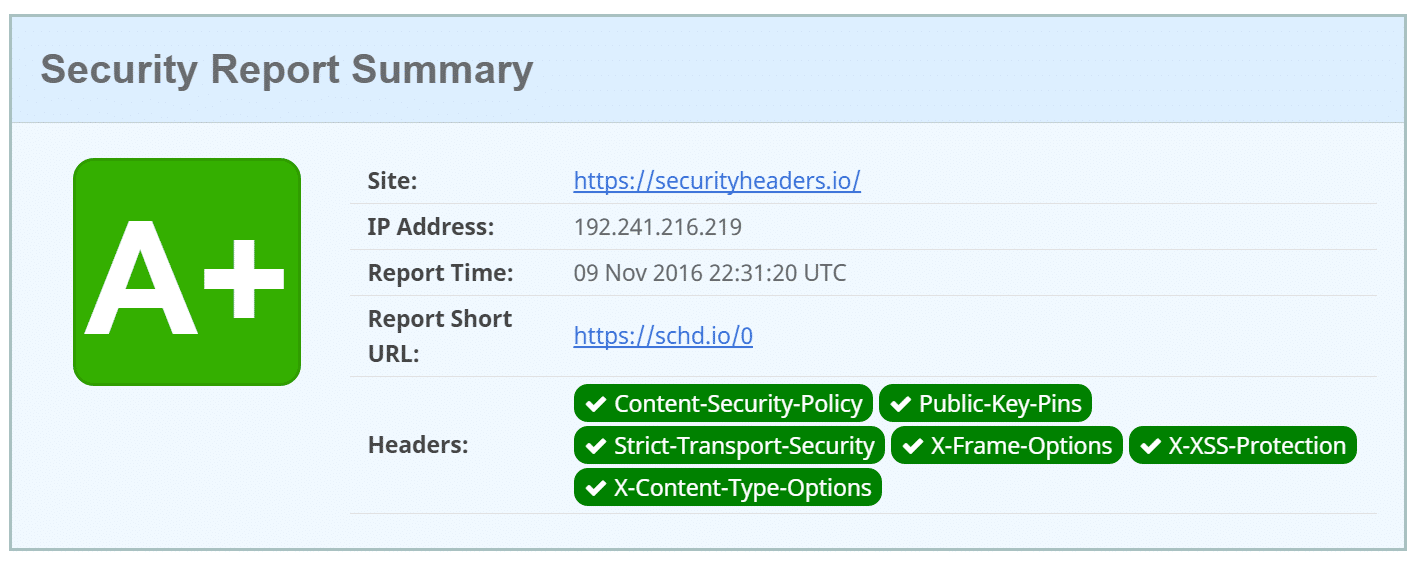
You can also scan your WordPress site with a free online tool like securityheaders.io which will let you know if the strict-transport-security header is being applied or not.
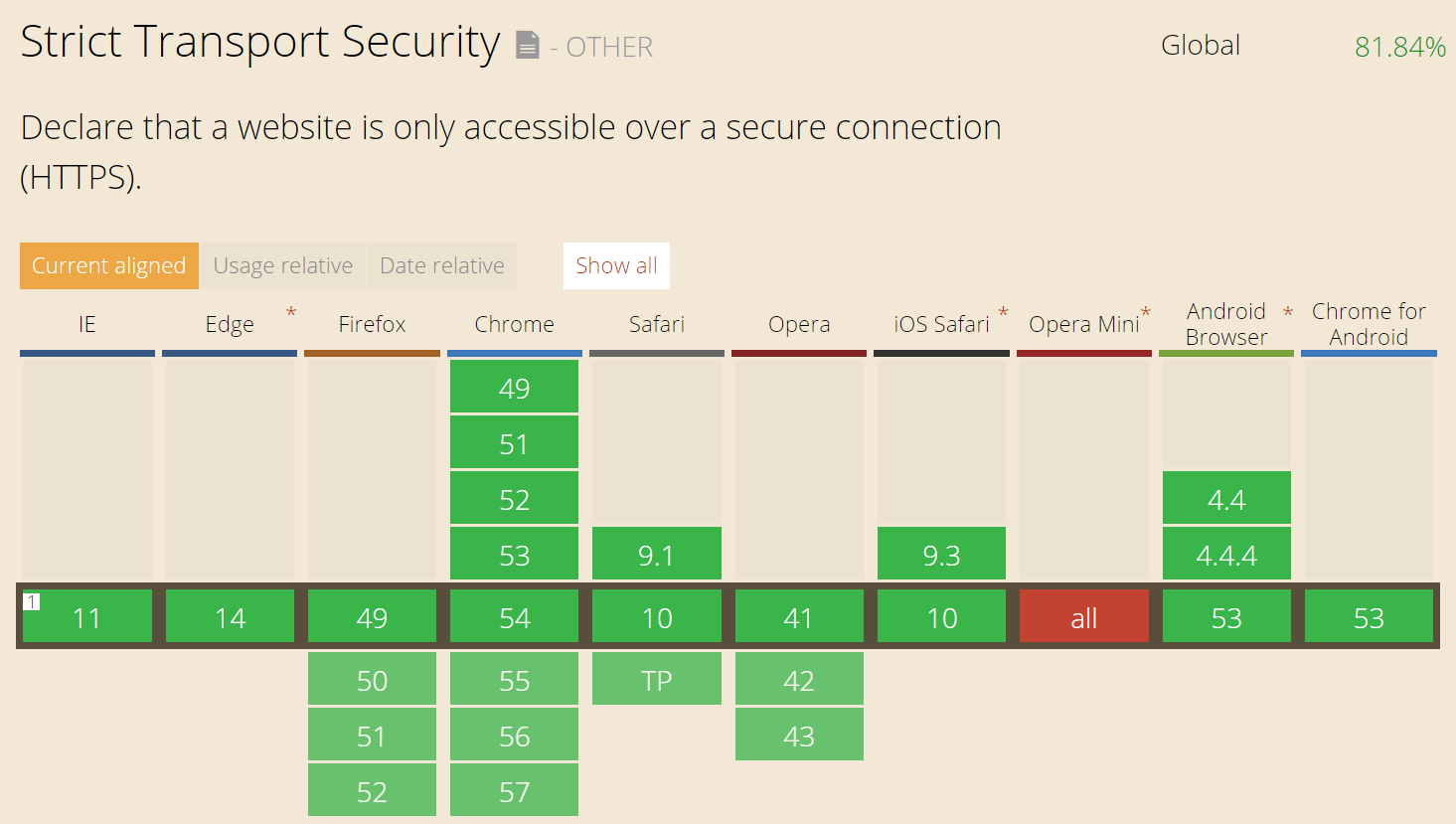
HSTS Browser Support
According to Caniuse, browser support for HSTS is very strong at over 80% globally and over 95% in the United States. Support for HSTS in IE11 was added in 2015 and currently the only modern browser that doesn’t support it is Opera Mini.
We also recommend checking out this article from Tim Kadlec on HSTS and Let’s Encrypt.
HSTS Impact on SEO
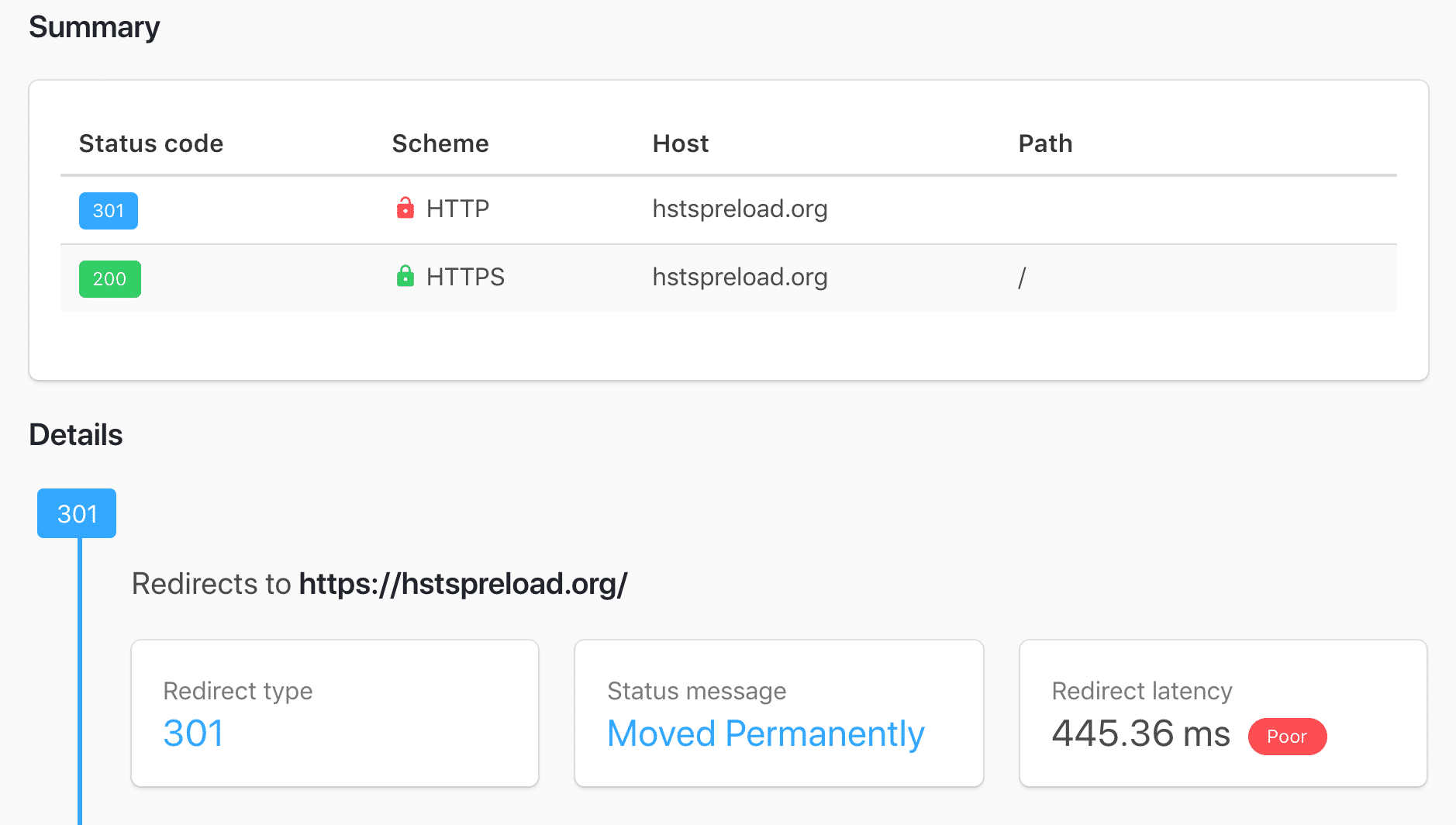
After your website is approved and included in the HSTS preload list, you might notice warnings from Google Search Console or other third-party SEO tools about 307 redirects. This is because when someone attempts to visit your site via HTTP a 307 redirect in the browser now happens, instead of a 301 redirect (as seen below).
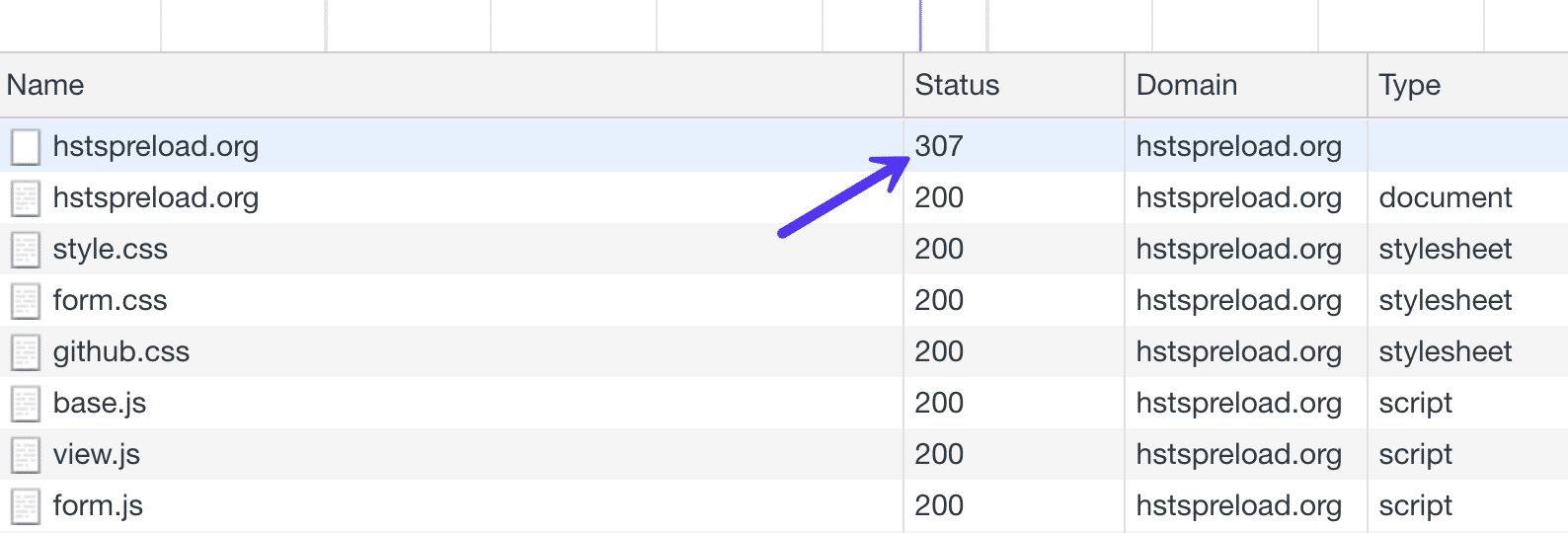
Typically a 307 redirect is only used for temporary redirects. A 301 redirect is used for URLs that have been permanently moved. So shouldn’t it be using a 301 redirect? And what about the SEO ramifications of this?
Well, in fact, a 301 redirect is still happening behind the scenes. The 307 redirect is happening at the browser level, not the server level. You can run the site through a tool that checks the redirect at the server-level, like httpstatus, and you’ll see that in fact, a 301 redirect is still happening. Therefore, you don’t need to worry about the HSTS header impacting your SEO.