You’ve probably heard the term “premium DNS” thrown around before and maybe you didn’t give it a second thought. Most people know that using a premium DNS provider can help them but don’t take the initiative to implement it, or perhaps don’t know how.
On October 21, 2016, the largest DDoS attack in history occurred, bringing down large companies such as PayPal, Spotify, Twitter, Reddit, and eBay. Some are even calling it the DNS Doomsday of the internet. Today we want to dive into how a premium DNS provider can help you in situations like these, if set up correctly, and prevent your WordPress site from going down.
- What is DNS?
- The DNS Attack that Affected the Entire Internet
- Premium DNS Provider Benefits
- How to Set up Premium DNS With Kinsta
What is DNS?
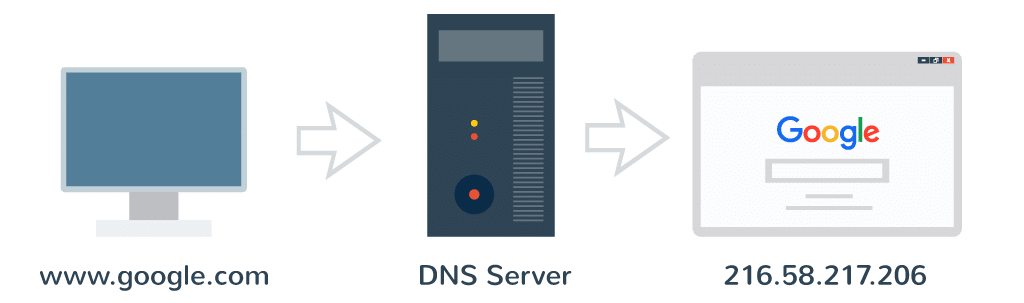
DNS (Domain Name System) is the backbone of the internet. You can think of it like a phone book for the world wide web. Every website and domain you visit are all mapped to an IP address.
When you type Google.com into your address bar, a DNS query is performed by your ISP to request the nameservers associated with the domain. The mapping to the IP address is then done behind the scenes by the server which allows you to then use the domain name to access it. Without DNS you would have to type something like 216.58.217.206 to get to Google. Wouldn’t that be fun!
When you register your domain, the domain registrar will typically provide free DNS services. For example, NameCheap, GoDaddy, etc. all provide you with the ability to setup your nameservers and route your domain to the IP address of your web host. A couple other popular free DNS providers include Cloudflare and Hurricane Electric Internet Services. Check out this list of 10 free DNS providers for other alternatives.
However, if you are serious about your business and website we highly recommend going with a premium DNS provider, which we will go into more detail below.
The DNS Attack that Affected the Entire Internet
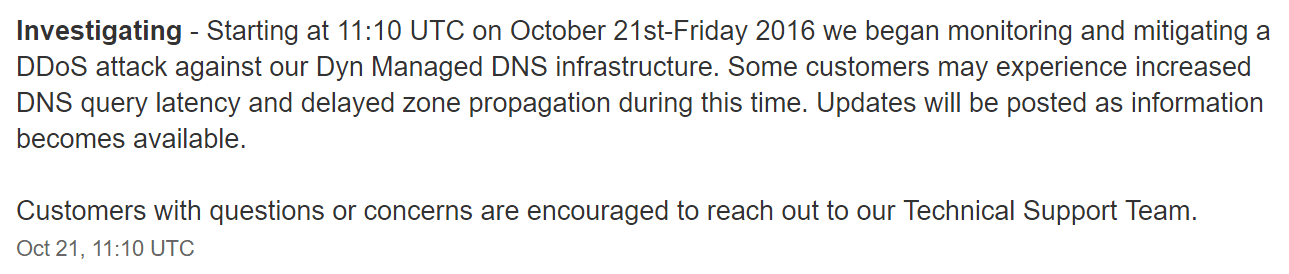
On October 21st, 2016, the worst possible thing happened for a lot of companies. A large distributed denial of service (DDoS) attack broke out against a popular premium DNS provider, Dyn, and managed to start taking services and sites offline.
Basically what happened is that they managed to take down Dyn’s nameservers, and as we explained above, without those the DNS lookups begin to fail. Dyn started reporting on this on their official status page and managed to provide consistent updates throughout the entire attack which lasted for approximately 11 hours.
https://twitter.com/Dyn/status/789503406842998784
Below is an example of what one of Dynatrace’s SaaS customers was seeing on Friday the 21st from their DNS monitoring application. The attack was focused on the East Coast but it rippled throughout the entire United States and Europe.
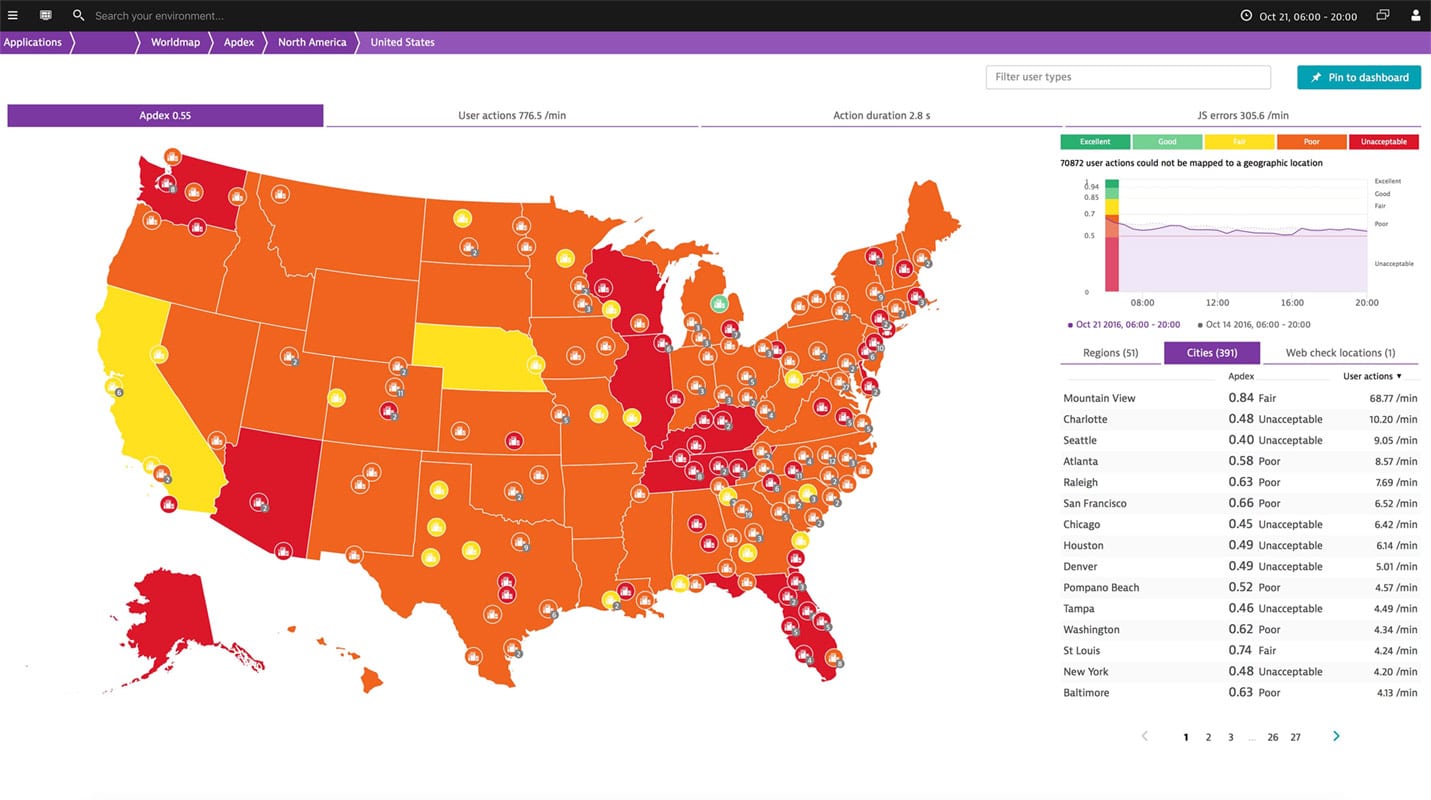
Companies affected included big names such as Twitter, Amazon, Github, Shopify, Weather.com, Basecamp, Freshbooks, SoundCloud, Spotify, Netflix, Reddit, Disqus, PayPal, and hundreds of others. We even noticed it here at Kinsta as Intercom, our ticket and chat support system, was also affected. The attack has now been attributed to the Mirai Botnet, which is a network of devices infected with self-propagating malware which used masked TCP and UDP traffic over port 53.
Because of what happened companies need to rethink their DNS strategy. Setting up a secondary DNS provider as a failover can help provide redundancy when issues like the above happen. And if anything, we at least recommend using a premium DNS provider, as opposed to a free one as they are more equipped to handle these issues. While attacks of this massive scale are rare, DDoS attacks in general, are not. In fact, according to data provided from easyDNS, DDoS attacks over time are getting much worse.
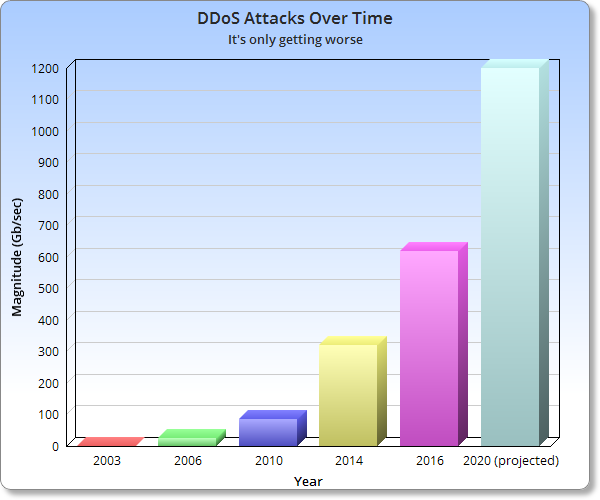
Even as of writing this article on October 31st, 123 Reg, a large domain registrar, was battling a DDoS attack against their DNS. You can expect in the years to come this will only increase.
Premium DNS Provider Benefits
There are a lot of good free DNS providers out there, but premium DNS providers offer a lot of advantages to ensure your website stays online; such as security, DNS failover, and better performance.
1. Security – Better Equipped for Large-Scale Attacks
Large premium DNS providers are typically better equipped for protecting you from large-scale DDoS attacks such as the one on Friday the 21st. Dyn is a very reputable company and even though there was downtime, they did their best to keep customers informed and worked around the clock to get everything back up. It is important to remember that the attack was the largest ever recorded at 600 Gb/Sec. If that same attack had occurred against a free or smaller DNS provider, you can safely assume the results would have been even more catastrophic for its customers.
Scott, EVP at Dyn issued an official statement on October 26th:
This attack has opened up an important conversation about internet security and volatility. Not only has it highlighted vulnerabilities in the security of “Internet of Things” (IOT) devices that need to be addressed, but it has also sparked further dialogue in the internet infrastructure community about the future of the internet. As we have in the past, we look forward to contributing to that dialogue.
2. Failover DNS Strategy
Companies now need to re-think their DNS strategy and have a failover in place. Brian Armstrong, co-founder at Canopy, wrote a great article back in 2014 titled “You’re probably doing DNS wrong, like we were.” This was after a DDoS attack had taken down their DNS provider, DNSimple. He touches on the issue of TTLs and that companies should make them longer. TTL means time to live, or rather how long it will stay alive in cache before it is cleared. For example, if you had a TTL of a week, and your DNS provider went down for a day it is more likely that users wouldn’t be affected because your ISP has the DNS cached.
However, there is also a flipside to using high TTLs. On Friday the 21st, if you went to add a 2nd DNS provider, it wouldn’t have mattered much because the TTL was set to expire in days or weeks not minutes. This can be resolved by simply setting up multiple DNS providers ahead of time in preparation. So yes, high TTLs can be good, but they should be used in combination with a multiple DNS provider failover strategies. Check out this more in-depth article about DNS TTL settings.
The community must work together to come up with commercial or open source solutions to make DNS configurations compatible between vendors (this is for complex DNS setups like failover, geo load balancing, etc.). This is a no longer a nice-to-have, but a must-have. – Catchpoint
There are a lot of premium DNS providers that have tutorials on how to setup secondary DNS as a failover. The recommended configuration is to set up redundant nameservers with multiple DNS providers.
- Secondary DNS with Dyn
- Secondary DNS with DNS Made Easy
- Secondary DNS with DNSimple
- Secondary DNS with easyDNS (and Amazon Route 53)
It is also important to note that depending on how you set up your secondary DNS it might hurt or help your DNS performance. DNS Made Easy has a great webinar explaining this a little more in-depth.
3. Performance
Another advantage of premium DNS is speed! Typically the free DNS provided by domain registrars like GoDaddy and Namecheap is very slow. DNS providers typically work just like a CDN, they have multiple POPs around the globe. Large DNS providers out there like Amazon, Cloudflare, Dyn, and DNS Made Easy all have massive infrastructures specifically designed for DNS with low-latency environments.
We ran a couple tests with the SolveDNS speed test tool. Here is an example of a domain using NameCheap’s free DNS and the response times.
Free NameCheap DNS
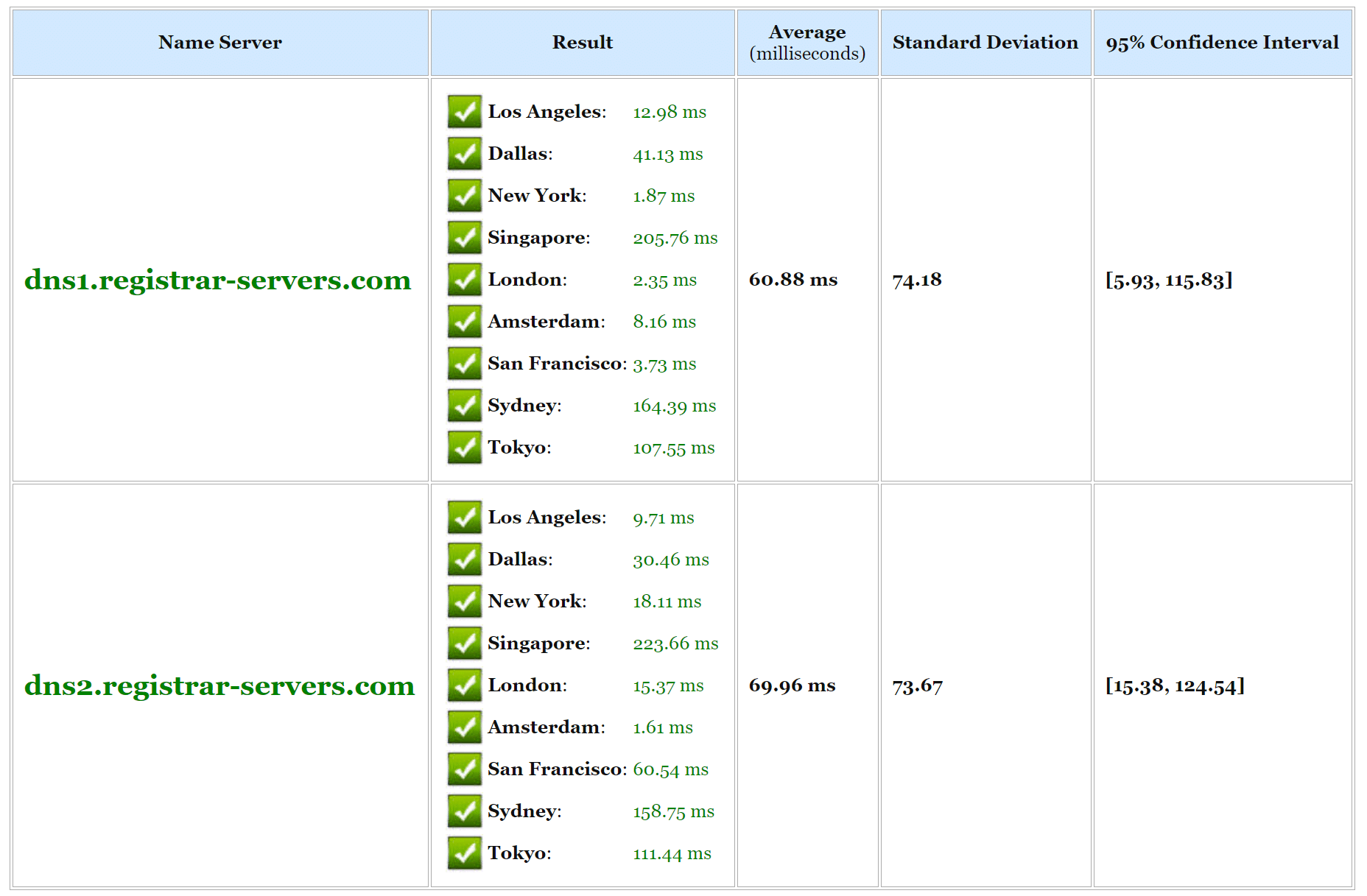
And below is an example using Amazon Route 53’s premium DNS. As you can see in general, DNS lookup times are much faster with Amazon. You can run your own tests against providers, but it is simply important to remember that just like with web hosts, there are faster ones and slower ones. Typically premium DNS providers will have better speeds. Cloudflare is a free one that also has great performance, however, they are tricky when you get into running multiple DNS providers.
Amazon Route 53 DNS

How To Set up Premium DNS With Kinsta
We believe premium DNS is important and that is why we partnered up with Amazon Route 53, a global Anycast network. They offer DNS failover as well as latency and geolocation routing to help ensure your website is always online and stable. The routing is especially important as it makes sure that your DNS is routed to the nearest location with lowest latency. Amazon Route 53 premium DNS is included for free for all Kinsta customers. To set it up on your WordPress site just follow the steps below.
Step 1
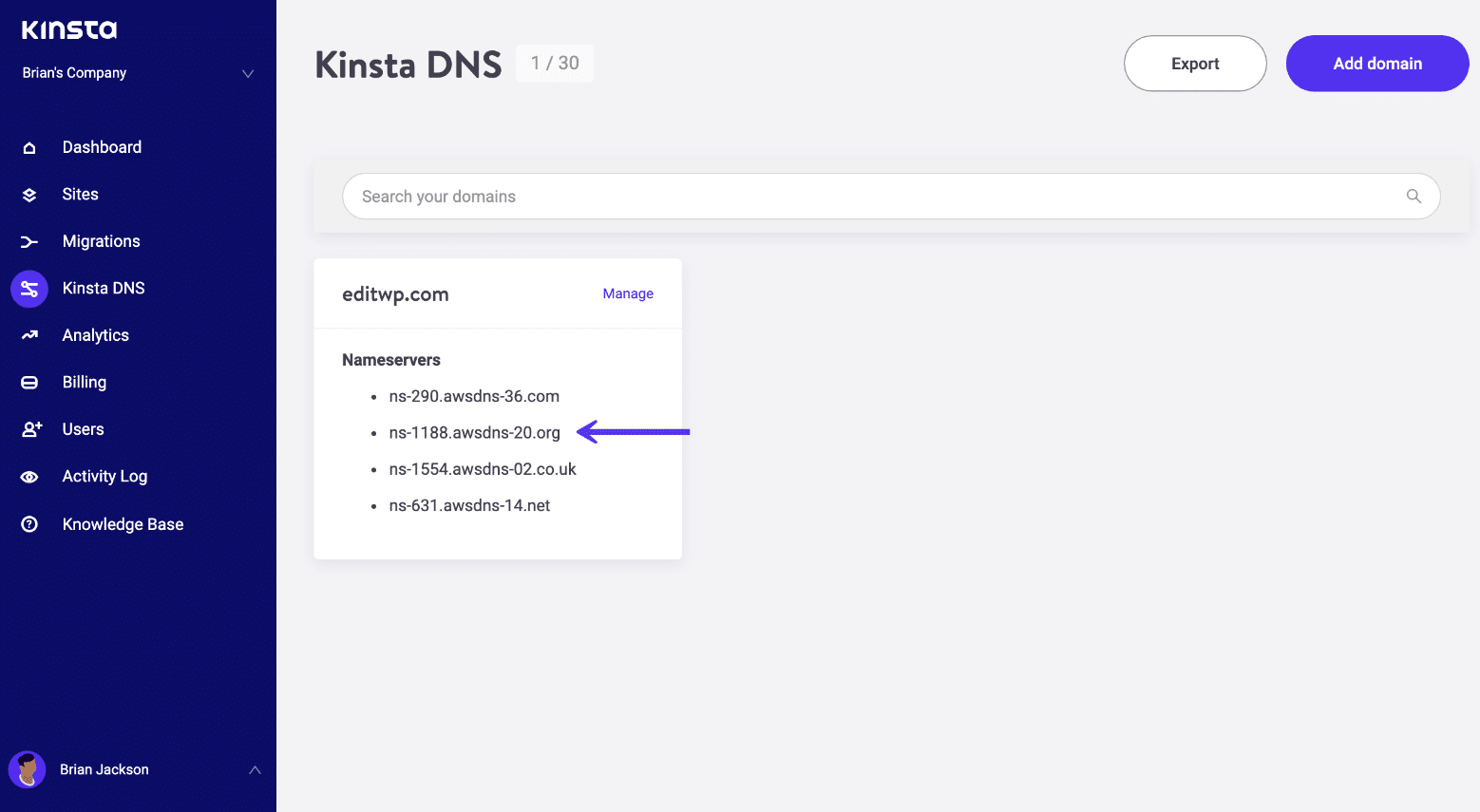
In your MyKinsta dashboard click into “Kinsta DNS.”
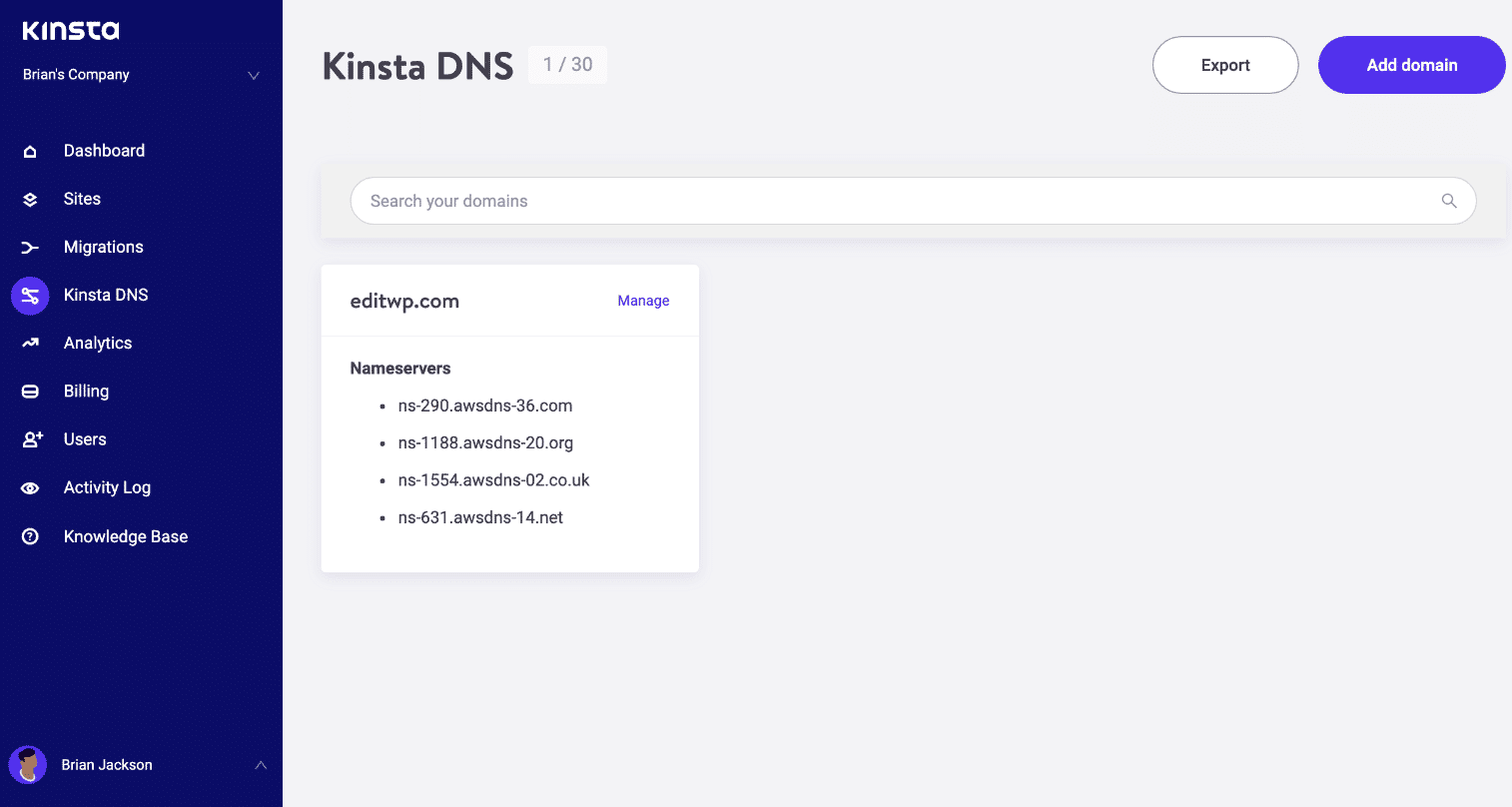
Step 2
Click on “Add Domain” at the top right.
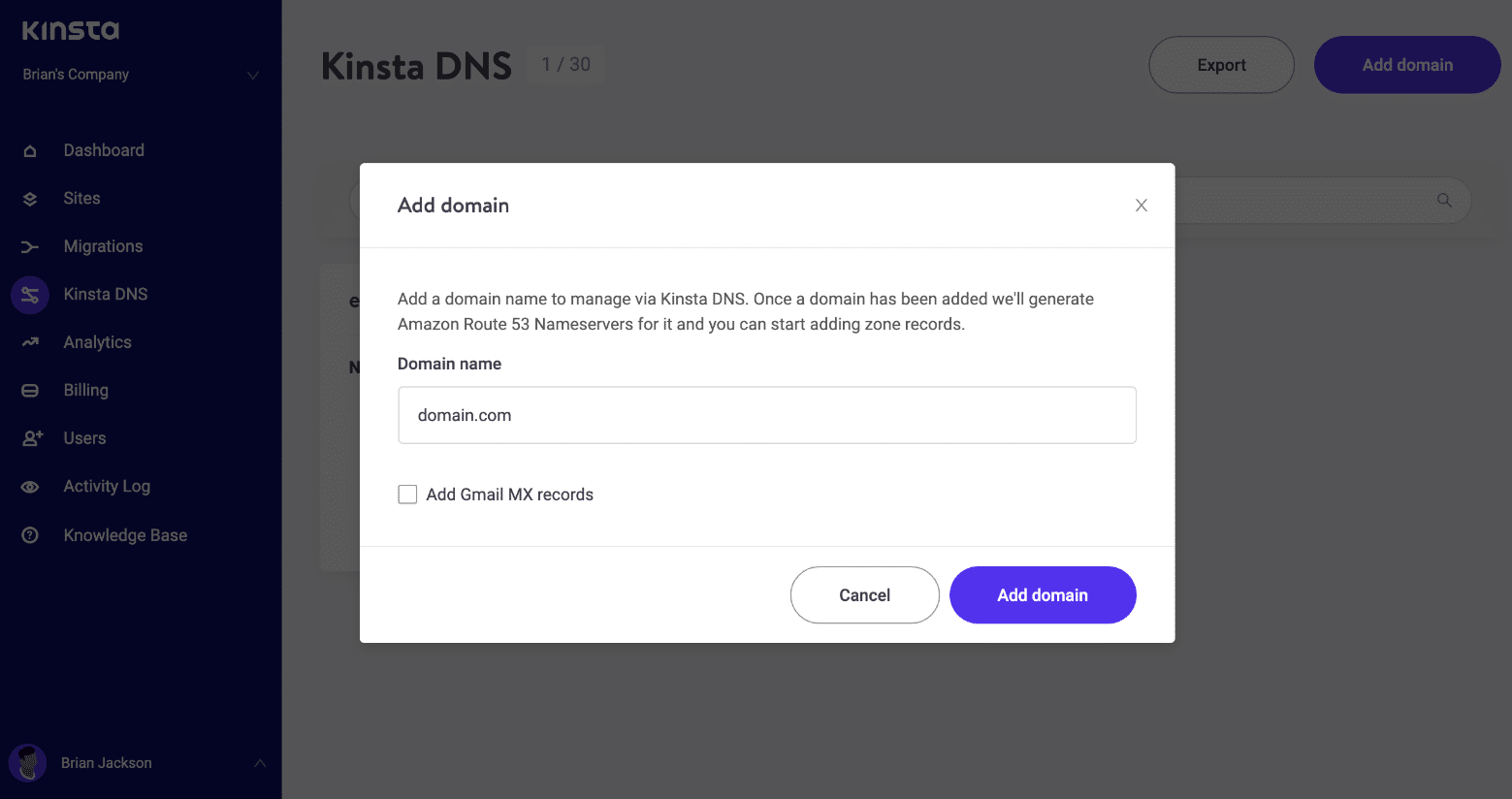
Step 3
You can then add your DNS records by clicking on “Add Record” at the top right. Your A record needs to point to your Kinsta IP address. Records supported:
- A
- CNAME
- MX
- SPF
- TXT
- SRV
- AAAA
- DKIM
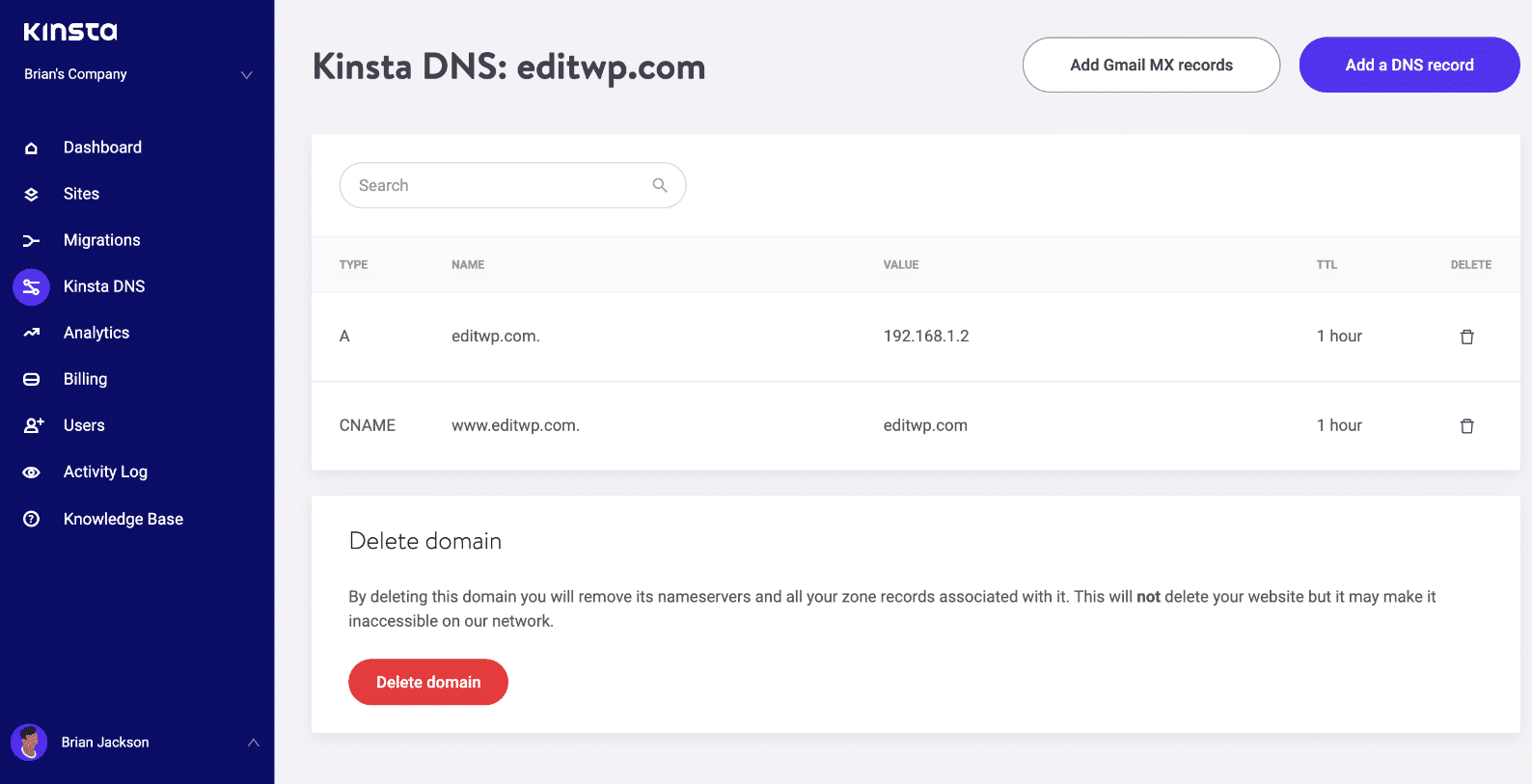
Step 4
You will then need to add Amazon’s nameservers with your domain registrar or 3rd party DNS provider. You can access these by clicking into Nameservers on the DNS records page.
And that’s it! Your DNS is now served via Amazon Route 53.
Summary
Just like Catchpoint and the EVP at Dyn both mentioned above, the recent incident has companies rethinking their DNS strategies and web security in general. Some companies lost millions of dollars from the downtime that happened on Friday the 21st. Using a premium DNS provider and also implementing a DNS failover strategy with a secondary provider is more important than ever. It is just a matter of time until the next DDoS attack hits and you should be prepared.
Have any of your own thoughts on using premium DNS providers? If so, let us know below in the comments.