A security technology like Sender Policy Framework (SPF) can prove invaluable in a world plagued by online attacks and spam messages.
Cybersecurity is a major concern for everyone, from individuals and businesses to government entities. Security risks such as email spoofing, phishing attacks, spam, and other malicious schemes have become rampant, targeting data, applications, networks, and people.
As a result, site owners can suffer in terms of lost data, money, reputation, and customer trust. And emails are one of the easiest routes of attack.
SPF is a popular email validation technique that can help ward off these attacks by detecting email spoofing and preventing spam. Using an SPF record can also help prevent your emails from being flagged as spam by other servers before reaching your targeted audience.
In this article, we’ll discuss SPF records and why it’s essential to implement this technique for email security.
Check Out Our Video Guide on SPF Record
What Does SPF Mean?
Before we get to what an SPF record is, let’s understand SPF first.
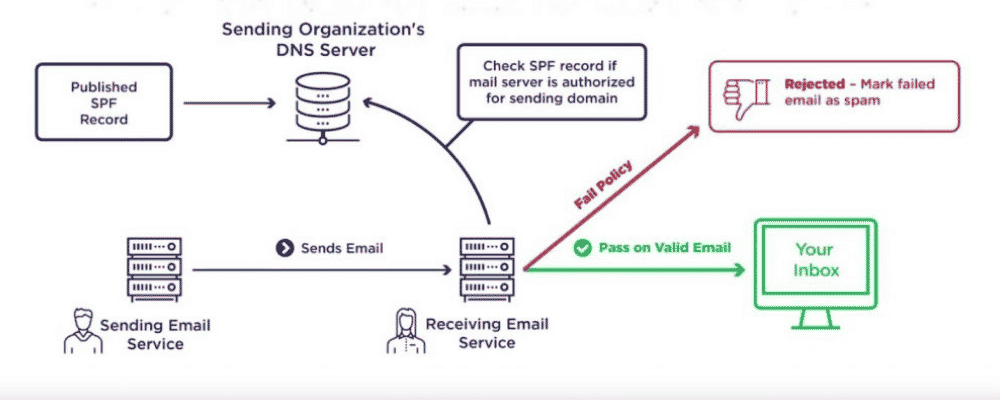
The Sender Policy Framework (SPF) refers to a method of authenticating emails that is designed to spot forged sender addresses during email delivery.
Attackers often spoof sender addresses, making them look genuine, like a regular user’s address. SPF can help spot these messages and quarantine them, derailing them from their attacks.
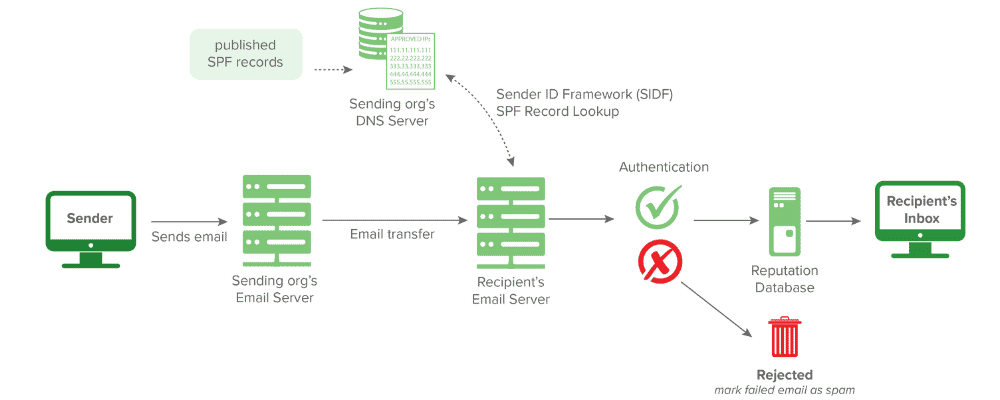
SPF allows the server on the receiving end to check whether an email appearing to come from a given domain is actually originating from an authorized IP address of that domain. The list containing all the authorized IP addresses and hosts for a specific domain can be found on that domain’s DNS records.
What Is an SPF Record?
An SPF record is a kind of TXT record published in a DNS zone file, containing a list of all the authorized mail servers that can send emails on behalf of your domain. It is an implementation of SPF that must be added to your DNS to help identify and mitigate spammers from sending malicious emails with forged addresses on your domain’s behalf.
Spammers carry out email spoofing by creating an email using forged sender addresses since most email servers don’t perform authentication. They then edit an email’s sender address by falsifying email headers, making it look genuine like the emails are sent from your domain.
This process is called spoofing, and it allows spammers to con the users and gain their private data and cause reputational damage.
Today, almost all malicious emails carry fake addresses. As a result, the people whose email addresses the attackers have stolen suffer reputation damage, waste time in fixing bounced messages, get their IP addresses blacklisted, etc.
Therefore, setting up SPF records is necessary to improve your email deliverability and security.
SPF Record Syntax
In general, an SPF record is defined using a type of TXT record (not to be confused with the legacy SPF file type record).
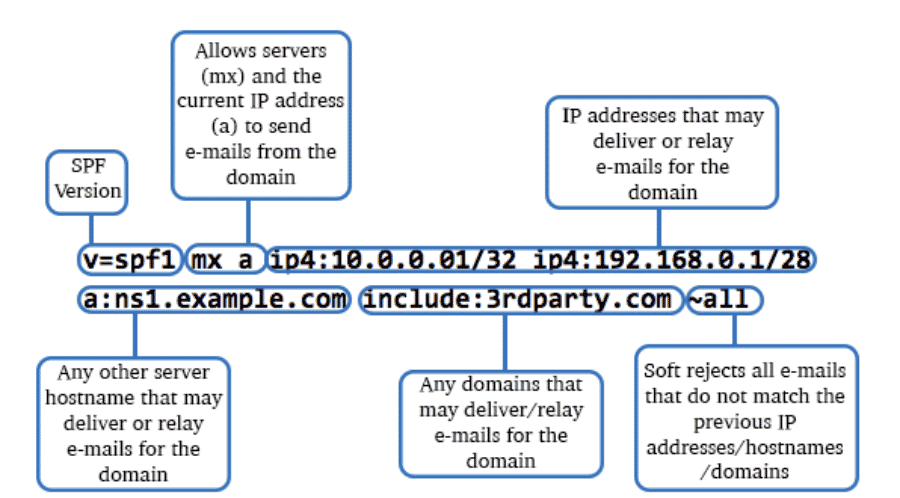
An SPF record starts with a “v,” indicating the SPF version used. Currently, this version must be “spf1” as it’s recognized by the widest range of mail exchange servers.
After this, other terms follow that define the rules for hosts sending emails from the given domain. These terms may also provide more information for SPF record processing.
Example of an SPF Record
Here’s what an SPF record looks like and what each portion of it means:
v=spf1 a include:_spf.google.com -all
v=spf1is the SPF version 1, a component that identifies a TXT record as an SPF record.aauthorizes the host detected in the A record of the domain to send the emails.include:is used to authorize emails that the sender can send on behalf of a domain (here, google.com).-alltells the receiver’s server that the addresses not listed in this SPF record are unauthorized to send any email. It also tells the servers to reject such addresses.
How Does an SPF Record Work?
Any computer can send emails claiming to come from any addresses as allowed by the SMTP. Attackers and scammers exploit this by using forged addresses, which are difficult to trace.
A similar technique is used in phishing attacks, where the attackers trick users into revealing their personal or business information by imitating a genuine site or service the users frequently.
To counteract this, SPF enables a domain’s owner to define which computers have the authorization to send emails from that domain, using DNS records. Additionally, the receivers can reject an email from an unauthorized source after verifying its address from the SPF records, before they receive the email’s body.
As we saw in the example above, an SPF record is in the form of a TXT entry listing all the IP addresses of authorized email servers for you. You can have one or multiple authorized IP addresses set up to send emails in an SPF entry.
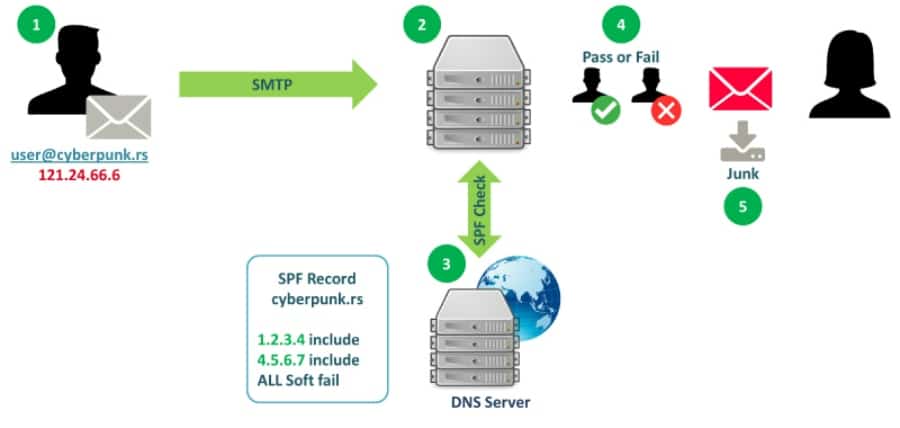
When an authorized user sends an email with an SPF record enabled, the recipient’s mail server performs a DNS lookup to spot the TXT entry and determine whether the sender’s IP address is authorized.
If it finds no SPF record, then it would send a “hard fail” or “soft fail” message to the sender.
If the receiver’s server rejects that domain, the unauthorized user or client must get a rejection message (“hard fail”). But if the client happens to be a message transfer agent (MTA), in this case, a bounce email to the actual envelope-from address will be generated (“soft fail”).
Components of an SPF Record
SPF records are made up of several different parts, starting with the version number.
Version Number
All SPF records begin with a version number, which must be authorized by mechanisms defining valid senders. The SPF version number, such as spf1, is followed by a string comprising mechanisms, quantifiers, and modifiers.
Mechanisms
Mechanisms describe the hosts designated as authorized outbound mailers for a given domain. An SPF record can have zero or multiple mechanisms. Some of the common mechanisms in SPF records are:
a: Specifies all the IP addresses in a DNS A record (example:v=spf1 a:google.com -all). It is used at the last and defines the rule to handle a sender IP not matching any prior mechanisms.mx: Defines all the A records towards the MX record belonging to each host. Example:v=spf1 mx mx:google.com -allinclude:: Defines other authorized domains (example:v=spf1 include:outlook.microsoft.com -all). If the policy of that particular domain passes, then this mechanism will also pass. You need the redirect extension if you want to achieve full delegation with another domain’s policy.ptr: It defines all the A records towards the PTR record of each host (example:v=spf1 ptr:domain.com -all). However, you must avoid this mechanism, if possible.all: Matches all the remote and local IP addresses and is used at the SPF record’s end (example:v=spf1 +all).exists: This specifies domains signed out as an exception according to the definition SPF. When a query is run on a given domain, it will be a match upon obtaining a result. It’s used rarely and offers more complicated matches such as DNSBL queries.ip4: Used to define an IPv4 address, for example, v=spf1 ip4:192.0.0.1 -all.ip6: Used to define an IPv6 address, for example, v=spf1 ip6:2001:db8::8a2e:370:7334 -all
These define all the IP addresses that are authorized to send emails from the domain.
Quantifiers
Mechanisms have a quantifier to define how they can handle a match.
An email server compares the sender’s IP address against the list of the authorized IP addresses in the mechanisms. When it finds a match for the IP address in one of the SPF mechanisms, it will implement the rule for result handling. And the default rule for this is pass or +.
The four quantifiers are as follows:
+represents the PASS result. If the address passes the test, the message must be accepted (example:v=spf1 +all). You can omit it because, for instance,+mxandmxare the same.-is for HARDFAIL, instructing that the address has failed the test and the email must be rejected (example:v=spf1 -all).~represents SOFTFAIL and is pronounced as a tilde. It means the address has failed the test; however, the result isn’t definitive. You can accept and tag a non-compliant email (example:v=spf1 ~all).?stands for NEUTRAL where the address has not failed or passed the test and you are free to accept or reject it (example:v=spf1 ?all).
When you see no quantifier in an SPF record, it means that the +all quantifier is applied.
Modifiers
Modifiers let you extend the framework. They are value or name pairs separated by the = sign and provide more information. SPF records can also have zero, one, or two modifiers, but they can appear once only, towards the end of the record.
The two most widely used modifiers are:
redirect: Used to send a query to other domains. This modifier is easy to understand compared to other mechanisms and modifiers and is used when you have several domains and need to use the same SPF record everywhere.exp: Used to provide an explanation when a FAIL quantifier is included on a matched mechanism. This explanation will be placed in the SPF log.
Why Do You Need SPF Records?
If your domain has an SPF record, it will decrease the chances of receiving malicious, forged emails, enhancing your email security and securing it against cyberattackers and spammers.
An SPF record also increases your domain’s credibility and reduces the chances of getting delisted by the spam filters. This helps legitimate emails find their way to you more quickly.
Furthermore, adding SPF records in your domain has become increasingly crucial to verifying which senders can send emails on behalf of your domain. It offers many benefits, which we’ll explore next.
Increased Email Security

SPF records help increase email security for individuals and businesses alike. In the age of cybersecurity, where users from across the globe are affected by cybercrimes, you must take steps to protect your inbox.
Adding SPF records is a way to do just that. By making it more challenging for email attackers to get through, spam messages are less likely to land in your inbox; hence, your email security increases.
Improved Email Deliverability
If a domain doesn’t have an SPF record, its emails can bounce, or servers may mark them as spam. And if this happens repeatedly, its ability to send emails successfully to its audience (also known as deliverability) reduces.
This becomes a roadblock for individuals and businesses using such domains to reach their targeted customers, employees, vendors, and other associated people.
Enhanced Domain Reputation

If your users constantly receive emails from attackers posing as your company, your domain’s credibility is at risk. Bad actors can also harm your customers and employees by exposing their personal details, which will further harm your reputation.
This is why it’s essential to protect your domain from such incidents with the help of SPF records. By restricting the sending of emails to only authorized IP addresses listed in the records, you’ll prevent spam messages and reduce the likelihood of such attacks.
DMARC Compliance
The email verification system DMARC ensures that only authorized users send emails on your domain’s behalf.
Its policies also instruct servers on how to handle emails with failed DKIM and SPF checks. DMARC instructs that such emails must be marked as rejected, spam, or delivered.
It also empowers domain administrators to receive reports highlighting email activities and make adjustments to their policies accordingly.
Who Requires an SPF Record?
You need to set up an SPF record for your domain if you send commercial and transactional emails to your customers, employees, or vendors. Using different email security solutions makes your email deliverability and security strong.
- Business and individuals: With an email authentication technique like SPF records in place, businesses and individuals can verify whether an email is sent on behalf of their domain or somebody is doing it for their personal gains and conning your associates. And you can make that even stronger by using SPF records with DMARC or DKIM to specify a full authentication policy for all your emails.
- ISPs: SPF records are beneficial for ISPs. If they haven’t set up an SPF record properly, they might have to perform email filtering again. Also, a failed authentication tells that there is a possibility that their emails are being blocked or recognized as spam by many servers.
Hence, if you want your emails to successfully reach the intended destination, using SPF records will ensure you of this and provide better security to your domains and emails. It will filter forged emails of phishers and spammers and protect your reputation.
How To Create, Add, and Edit SPF Records
Here’s how you can add, create, and edit your SPF records.
How To Create an SPF Record
Before you start creating an SPF record, it’s necessary to understand if your email sending setup requires you to do it in the first place.
So, first, understand the Return Path. SPF revolves around the domain used in the Return-Path, instead of the FROM domain. Therefore, in the beginning, figure out the Return-Path in use for your mail sending.
Also, certain email sending services (ESPs) like Google can use your domain name in their Return-path. This requires you to create an SPF record of your own for your domain.
However, other ESPs, such as Postmark, can use their domain in the Return-path where you don’t require setting up an SPF by yourself; your ESP must do it instead.
So, now that you know why you need to set up an SPF record, let’s understand the step-by-step process of how to do it.
Step 1: Identify IP Addresses That Send Emails
Organizations can have multiple places from where they send an email. So, in the first step to creating an SPF record, you must identify which IP addresses you use from your domain to send the emails. List all your IP addresses and corresponding mail servers in a text document or spreadsheet.
In addition, find out what all avenues are used for sending emails on your brand’s behalf. It could be a web server, an in-office email server like Microsoft Exchange, your ESP’s mail server, a mail server belonging to your customer’s mailbox provider, or a third-party mail server.
But if you are unsure of your IP addresses, you can contact your ESP and get the complete list containing all the IP addresses related to your account. Another option could be discussing this with your System Administrator. They can list all the IP addresses used by your business.
Step 2: List the Sending Domains
An organization can own many domains. Out of this, they can dedicate some of their domains to sending emails and others for different purposes.
In step number 2, you will need to create an SPF record for each domain you own, whether or not the domains are used for emails or any other purpose.
This is because cybercriminals may try spoofing the other domains that you might not be used to send your emails since they won’t be protected with SPF while others used for sending emails are.
Step 3: Set Up the SPF Record
SPF compares the IP address of the sender mail server to a list containing authorized sender IP addresses published by the sender in their DNS record to validate a sender’s identity and keep your emails secure.
To create an SPF record, you must write a v=spf1 tag, followed by the IP addresses authorized for sending emails. Example: v=spf1 ip4:192.0.0.1 -all
Furthermore, in case you use a third-party solution to send emails on your domain’s behalf:
- Add
includein the SPF record to specify that the third party is a legit sender. For example, you can write:include:google.com - After adding all the authorized IP addresses associated with your domain, end the SPF record with a tag — either
-allor~all.Here, the-alltag signifies a HARD SPF FAIL while the~alltag signifies a SOFT SPF FAIL. However, for leading mailbox providers both-alland~allwill result in an SPF failure. But in general,-allis used frequently since it is more secure. - Create your SPF records in such a way that it doesn’t exceed 255 characters and avoid adding more than 10 include statements, also known as “lookups.”
Now, your SPF may look something like this:
v=spf1 ip4:192.0.0.1 include:google.com -all
This is for your domains that are authorized to send emails on your behalf. But for your other domains, you must exclude modifiers (except -all) in the SPF record.
Here’s how your SPF record might look for domains that you don’t use for sending emails: v=spf1 –all
This is how you can create your SPF record. After that, simply publish it.
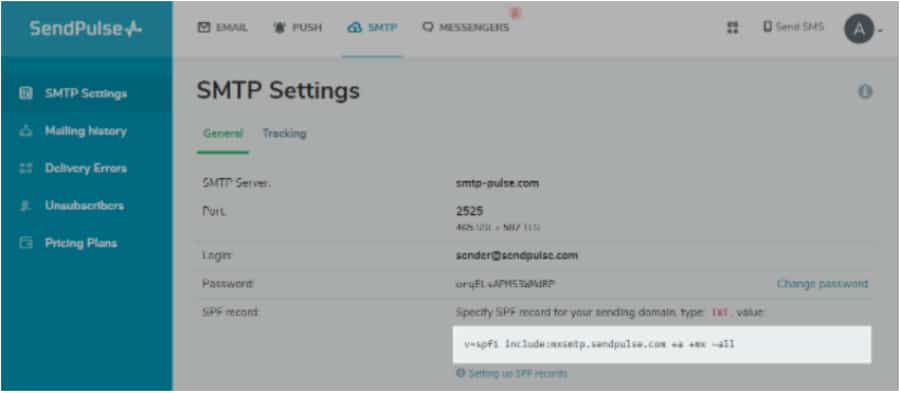
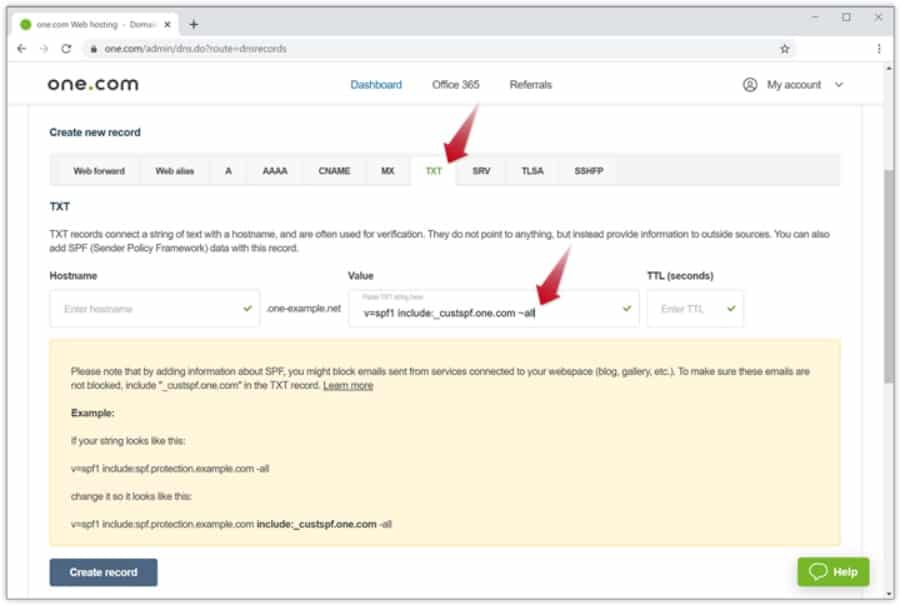
Step 4: Publish the SPF Record
Once you have defined the SPF record, the next step is to publish it in your DNS. There are two methods to do this:
- Work with your internal DNS administrator and instruct them to publish the SPF record to your DNS. Your DNS provider will provide you with a dashboard that you can access and carry out the publishing task easily.
- You can directly ask the DNS service provider to publish your SPF record in the DNS.
This will enable the mailbox receivers such as Gmail, Hotmail, Mailbird, etc., to request the SPF record.
Moreover, if you want to update the DNS records:
- Log in to the domain account you have bought from your domain hosting provider
- Choose the domain whose records you want to update
- Go to the page where your DNS records are stored, which can be a DNS manager
- Create a fresh TXT record and define your domain’s name as the Host field
- Fill the “TXT Value” field with the SPF record and specify a Time To Live (TTL)
- Click on “Add Record” or “Save” to publish the new SPF record on your DNS.
Step 5: Test the SPF Record
After you have created your SPF record and published it, you can use an SPF record checker to test the SPF record. There are many options available in the market for SPF record checkers, such as Dmarcian, Agari, Mimecast, etc.
Performing a test will help you check the validity of your SPF record and see the list containing all the authorized servers that can send emails on behalf of your domain. If you can’t see a legitimate IP address listed, you can include the sending IP address left and update your record.
How To Add an SPF Record to Your Domain
You must access your domain’s DNS control panel in order to add an SPF record. If you use a web hosting service provider, such as Kinsta, the process of adding an SPF record to your DNS will be simpler. You can reference documentation and follow the steps to do it.
In general, email service providers publish SPF records to enable sending emails from your domains. But if you don’t have an idea about it or your ISP manages your DNS records, you can forward this to your IT department.
Limitations of SPF Records
Although adding SPF records will provide you benefits in terms of email security, deliverability, and more, there are certain limitations to them. Let’s talk about those limitations.
DNS SPF Records
Earlier SPF versions were used to check for the settings in the sender domain’s DNS TXT records in order to facilitate faster deployment and testing. DNS TXT records were designed to be free-form text without any semantics attached to them.
However, a type-99 Resource Record was assigned by the IANA to SPF in 2005. This resulted in reduced usage of SPF since users were overwhelmed by the two mechanisms, which were confusing for them. In 2014, it was discontinued.
Header Issues
SPF was originally designed to prevent attackers from spoofing an email’s envelope-from address. But many are now only doing it in the mail header’s “From” field, which is visible to the recipients instead of being processed by their MTA. It increases the risks of spoofing.
Although you can use SPF with DMARC to check the mail header’s From field, you may need some advanced, stronger solution to stay protected from display name spoofing instead of SPF.
Besides, it is challenging to update SPF records if you add email streams or change your ISP. SPF records also can break the forwarding of a plain message, and it doesn’t guarantee email authentication.
SPF Records Best Practices
Before we discover the best practices for creating and maintaining SPF records, let’s first talk about some general practices.
- Your sending IP address must contain a PTR record. It works somewhat like an inverted phone directory that enables you to look up an IP address along with a hostname. However, public internet access points and residential IP addresses for internet connections often don’t have PTR records. It is used when there is a need to verify incoming connections.
- Use email authentication systems. You can use either one or all of the three email authentication systems: SPF, DMARC, and DKIM. Legitimate senders using email authentication could be easily recognized, compared to the ones who don’t use it and remain at a security risk from email spamming. Although using these systems won’t necessarily guarantee the successful landing of your emails to the destined inboxes, it will provide increased protection. This is better than not having any email security mechanisms to monitor and preserve the sender’s reputation.
- Never, ever use or include a record with
+allin it. The only way to productively useallis in the~allor-allmechanisms.
After these general practices, let’s talk about some of the SPF record best practices.
Use Limited SPF Records
SPF includes plenty of powerful and complex mechanisms, but it’s not necessary to use all of them in your SPF records. Keep your SPF records simple and define only the required number of SPF records, not more than that.
This holds true for the include: mechanism as well. Use it in a limited number and avoid nested includes if you can. It will prevent you from going over the limit of 10 DNS lookups. You can also add wide-ranging IP addresses at once, instead of doing it all individually. This simplifies the process and saves time.
Specify Ranges in CIDR Notation
Add the ranges in CIDR notation, because a single mistake can dramatically alter the value. So, if an attacker succeeds at compromising some of your systems and one of them holds the IP address belonging to this range, it could be fatal. They can misuse the properly authenticated IP address to send spam emails. It could damage your reputation, lead to data loss, and result in your domain being flagged as spam by mail providers.
Since this risk is hugely prevalent, mailbox providers have become vigilant and block domains that look suspicious to them in order to prevent such occurrences. They limit the allowed CIDR size ranges to be considered valid in SPF records.
Avoid Using +all Statement
Avoid using the +all statement in your SPF records. It may look overly permissive, and detecting this type of security issue is hard because these SPF records are syntactically valid. Even tools and testing solutions to check the records might not identify overly permissive records.
The +all statement enables the SPF record to literally permit the entire web to send emails on your domain’s behalf, including the malicious ones. In fact, domains involved in spam distribution often have SPF records terminating with +all. As a result, they can send spam emails containing malware infects from any IP address.
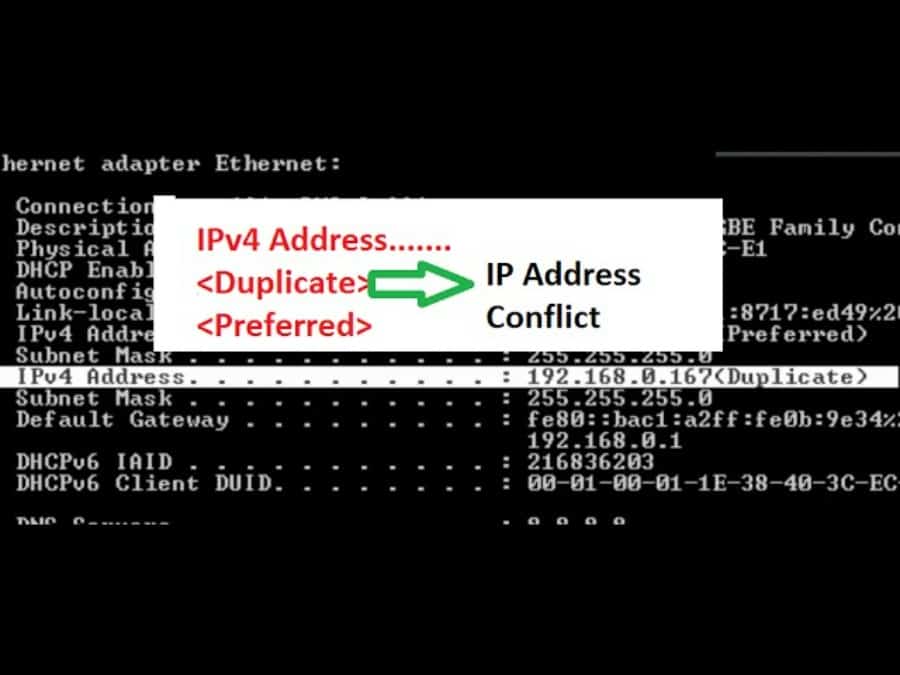
Beware of Duplicate Records
In general, domains have just one SPF record, meaning it can store only one TXT record beginning with the statement v=spf1. And if you try adding multiple records in a domain, it can lead to permanent errors.
This SPF limitation is violated frequently. Many try adding multiple records because they may have deployed various services in their domain, where each service provider might require them to create and add an SPF record to their domain.

Duplicate records damage your email deliverability, invite security risks, and can tarnish your reputation. Large mailbox service providers like Google and Microsoft have techniques to limit such damages and automatically fix duplicate records. But smaller email systems might not.
When you identify duplicate SPF records, you must immediately address the issue, which is fairly easy to fix. Organizations with several SPF records can merge them into one single statement. Combining two SPF records will ensure that v=spf1 remains at the SPF record’s beginning and appears only once, while all is kept at the end.
Character Limit
SPF records can have up to 255 characters for a single string, according to the RFC. This is a limitation for all TXT records in a DNS.
As explained before, any SPF records failing to comply with this guideline may involve permanent or temporary errors in recipient mail systems. Although your DNS manager might prevent you from going beyond this limit, it may result in issues while storing longer records.
Even though you can keep the records only 255 characters long in a single string, there is an option to create multiple strings in one DNS record. So, when a recipient mail server starts analyzing the SPF record and finds multiple strings in a record, it combines them in a specific order with no spaces.
Once this is done, the mail server would verify the content. Again, keep in mind that there’s still a limitation to the total number of characters in your record, even if you can add multiple strings. Understanding this limit could be challenging, but it ensures that DNS packets don’t exceed 512 bytes, which is a recommended UDP packet length.
However, if your SPF record exceeds this limit, create sub-records and split a single record into several records in order to prevent SPF verification issues. While splitting your SPF records, include each sub-record in the main part. Be careful since it could create an overwhelming number of DNS requests, which is a security problem needing remediation.
Limit DNS Lookups
Apart from keeping 255 characters in a string, you must also limit the number of DNS lookups. The RFC specifications instruct not to perform more than 10 DNS lookups in the record. It helps prevent issues like infinite DNS loops and Distributed Denial of Service (DDoS) attacks.
But what really happens when you do 10+ lookups in your record?
It will result in a permanent error during SPF authentication. SPF mechanisms — include:, a, PTR, mx, exists, and redirect — will lead to a DNS query.
However, the mechanisms — all, ip4, and ip6 — don’t count against a DNS query.
Furthermore, be aware of nested include statements such as sub-records that are used to disintegrate a larger record. This can increase DNS queries generated by your SPF record. So, when you use a third-party service, ensure they don’t use excessive DNS queries in SPF records.
Avoid Duplicate Subnets and IP addresses
All SPF entries resolve to a subnet or IP address.
Duplicate subnets and IP addresses can be easily generated while creating a list of IP addresses and systems authorized to send emails. Typically, this can happen when you add the include: statement in your SPF record as well as in the domain’s MX records for the mailbox service provider. These IPs could be the same, belonging to the included subnets.
The best practice to follow here could be using the ip4 or ipv6 notation, if the server’s IP address rarely changes. This will enable the recipients to avoid any DNS lookups. In addition, you can specify an IP address range if you have a long list containing outgoing email servers since DNS lookups for each SPF record are limited to ten.
Apart from these, you may consider a few more things:
- Use a limited number of
include:mechanisms, and avoid nested includes if you can. - Use the
~allor-allmechanisms, instead of the+allmechanism. - Avoid using the
existsSPF mechanism, because if you don’t use it properly, security risks may seep through the errors made during the process. - Try not to use the ‘ptr” and mechanism since it’s been deprecated in the latest SPF RFC draft.
- Avoid assigning the type of DNS record. This is no longer accepted in TXT records.
- When specifying address blocks via CIDR notation in the SPF records, use blocks between /30 and /16. The higher numbers after a slash mean smaller address blocks, which is better. Also, don’t use blocks between /1 to /15 since some recipients may ignore or discount them.
- Ensure to resolve all mechanisms using a domain in the SPF record. Oftentimes, system administrators don’t remove legacy systems like an exchange server located on-premise, which Office365 cloud services have replaced. Even though adding Office365 to the updated SPF records is required, removing the legacy system still might not have been updated. In this case, the domain in the SPF record is still present but in reality, it doesn’t exist anymore, leading to a temporary SPF failure.
- Use email authentication systems like DKIM and DMARC with SPF to make it more effective in protecting your domain. So, if you use DKIM and DMARC, it’s necessary to know the best practices for them as well.
Using DKIM With SPF
DomainKeys Identified Mail (DKIM) provides an encryption key and digital signature that verifies that an email message was not faked or altered. Since DKIM uses cryptographic digital signatures, you must follow some best practices to secure your domain.
- You must regularly change your cryptographic keys to prevent attackers from exploiting them. Many mail senders use old keys created years ago, which attackers can more easily exploit; for these, you must create a fresh DKIM key. You can also rotate the keys many times in a year, especially if you send thousands or millions of emails in a month to secure sensitive emails.
- Ensure you keep the length of your keys at least 1,024 bits because signatures created using keys less than that are often ignored. Hence, more and more senders are switching to keys that are 2,048 bits or even longer.
- If you are an ESP, don’t just use one DKIM key for all your customers. Assign them a new unique DKIM key for their emails.
- If you notice any bounced emails, sign them using DKIM.
Using DMARC With SPF
Domain-based Message Authentication and Conformance (DMARC) unifies the SPF and DKIM authentication mechanisms into a common framework and allows domain owners to declare how they would like an email from that domain to be handled if it fails an authorization test.
Using DMARC comes with many benefits. It provides you with a reporting feature and lets you signal mailbox service providers to block messages that failed authentication and are sent on your domain’s behalf. This helps identify and block fraudulent messages sent from your domain, which helps safeguard your customers and enhances your domain reputation.
So, if you don’t use DMARC yet, start using it immediately. And if you do, ensure your messages include “identifier alignment.” This alignment is essential for an email to pass DMARC’s verification. But if you don’t include it while using DMARC, it would send your emails directly to the suspicious list.
How To Check SPF Records
You can use some tools to check SPF records. These tools are known as SPF record checking tools or SPF record checkers.
SPF Record Checker
An SPF record checker helps ensure the validity of an SPF record by checking various parameters:
- Existence of the Record: This is used to confirm whether a given SPF record actually exists in a DNS or not.
- Multiple Records: A single SPF record is permitted in a DNS. So, an SPF record checker verifies whether only one record exists or multiple.
- Maximum Lookups: The maximum number of SPF lookups that must be done is limited to 10. Therefore, the SPF record checker finds out the total number of lookups and whether it exceeds 10 or not.
- PTR Mechanism: The tool verifies the usage of a PTR mechanism since it’s not recommended to use this mechanism.
Examples of SPF record checkers include Dmarcian, Agari, and Mimecast, among others.
Summary
As cybersecurity risks are evolving and affecting individuals and businesses alike, you must ensure to implement as many security layers as you can to remain protected. You can use many security techniques, tools, solutions, and services to protect your data, network, applications, and systems.
Adding an SPF record to your domain is one of those techniques that can help safeguard your business assets and reputation by preventing spammers from sending emails on behalf of your domain.
Using an SPF alone might not offer you complete protection; hence, use DKIM and DMARC with your SPF records. This strategy is more efficient in detecting security risks like email spoofing, getting blacklisted by servers, and being flagged as spam.
So, if you use these techniques, be sure to follow the best practices listed above for SPF records, DKIM, and DMARC, and make use of an SPF record checker to test the validity of your record.