A DDoS attack is surprisingly easy to carry out and affects millions of websites worldwide every year, with the number of attacks rising.
Suffering DDoS attacks may seem like an inevitable side effect of being online; the more successful your site, the more likely it might seem that you’ll be the target of an attack at some point. But you can reduce the chances of a DDoS attack affecting your site.
You might be wondering: What is a DDoS attack? And how can I protect my site from them?
In this post, we’ll explain what DDoS attacks are, explore what might make your site vulnerable, and outline the ways you can reduce their probability and impact.
What Is a DDoS Attack?
Let’s start by examining exactly what a DDoS attack is and, importantly, what it is not.
DDoS stands for distributed denial of service but is often referred to as a simple denial of service. A DDoS attack consists of a website being flooded by requests during a short period of time, with the aim of overwhelming the site and causing it to crash. The ‘distributed’ element means that these attacks are coming from multiple locations at the same time, as compared to a DoS which comes from just one location.
If your site suffers a DDoS attack, you will receive thousands of requests from multiple sources over a period of minutes or sometimes hours. These requests aren’t the result of a website suddenly getting a spike in traffic: they are automated and will come from a limited number of sources, depending on the scale of the attack.
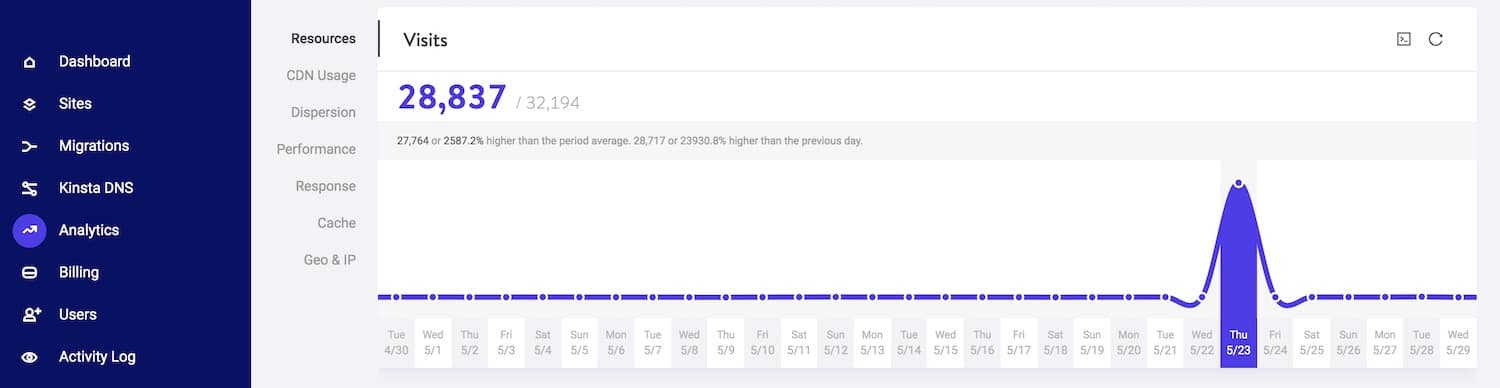
In the screenshot below, you can see the sudden spike in requests received by a site during a DDoS attack.
A DDoS attack isn’t the same thing as hacking, although the two can be linked; the perpetrators aren’t attempting to access your website’s files or admin, but instead, they cause it to crash or become vulnerable due to the volume of requests. In some cases, this will be followed by attempts to hack the site when it’s vulnerable, but in the majority of cases, the aim is simply to make the site stop working.
It may sound as if there isn’t any way to avoid a DDoS attack: after all, if someone decides to flood your site with requests, there isn’t much you can do to stop them.
But although you can’t do much to stop someone attempting to damage your site with a DDoS attack, there are steps you can take to ensure that if you are subject to an attack, your site won’t cease working and it won’t be vulnerable to hacking.
We’ll cover those steps later in this post, but first, let’s examine why someone might want to mount a DDoS attack on your site.
Why Would Someone DDoS your site?
So why would someone mount a DDoS attack on your WordPress site? What could they have to gain from it?
There are many reasons why an attacker might want to put your site out of action via a DDoS attack. These include attacks by competitors and attacks because of your content.
DDoS Attacks by Competitors
In an ideal world, your competitors would attempt to outperform you online by improving their content, SEO and conversion rate, which is the legitimate way to use your website to gain competitive advantage.
But in some cases, competitors might take more extreme measures. A competitor might hire someone to mount a DDoS attack on your site in the knowledge that this won’t only impact your website, it’ll also impact your business.
In the time it takes you to get your site working again, they will be taking business from you, especially if they are running ads using your business name as a keyword. If your site isn’t up and running again quickly, you’ll lose search ranking and may find that your competitors now rank above you on Google.
Of course, it’s very difficult to prove who carried out any DDoS attack. The attack won’t come from your competitor’s IP address! Unless you have very deep pockets, attempting to take legal action against a competitor you suspect of doing this is unlikely to be successful.
Far better to protect yourself from the effects of an attack in the first place. And don’t be tempted to mount another DDoS attack against your competitor in response. This is illegal and it’s far better to reassure yourself that a competitor desperate enough to use measures such as these probably won’t have the longevity or reputation that your business does.
DDoS Attacks on Your Content
Some sites are subject to DDoS attacks because of the nature of their content.
For example, a whistleblowing site might be subject to an attack. A site dealing with a controversial issue (such as access to abortion or anti-racism) might suffer attacks from people who disagree with its message and want to put it out of action. Or your content might be commercial but still sensitive and there are people who don’t want it available online.
If your site is successfully attacked, it will put your content out of circulation, which could cause problems for your users if they need access to information or guidance.
You’ll also be spending time resolving the issue, losing any revenue you might be making from the site (either in sales or donations if you are a nonprofit), and your rankings can drop if your site is returning a 502 error for hours or days.
Politically Motivated DDoS Attacks
Politically motivated DDoS attacks are becoming more common as cyber threats are increasingly used to disrupt the political process.
If your website is for a political party, candidate or organization, or advances a specific political cause, then it may be vulnerable to attack from people who disagree with your politics.
This won’t unnecessarily come from your political opponents. It is more likely to come from external sources that seek to disrupt political debate, block certain types of content and use chaos to confuse and disenfranchise people.
The attack could be an attempt to make it impossible for people to access your content (see above), or it could be a more personal attack on the individual candidate or organization behind the site.
This is different from a site becoming overloaded because of spikes in visits due to the news cycle. I once worked on the website of a political party which became overwhelmed when the party’s manifesto was launched for a general election. That was the first UK election in which e-campaigning was significant and we just weren’t prepared for the volume of traffic.
Instead, a DDoS attack will be much sharper and more abrupt, seeing a very sudden spike in requests for sometimes a matter of minutes. This will look very different from a natural spike in traffic, which although it can be sudden will normally take the form of a curve instead of a cliff.
If you are running a campaign (which might have made you more vulnerable because of the extra publicity), then it will be particularly important to ensure your site remains operational and not to waste time dealing with the attack when you could be focusing on campaigning activity. That’s why it’s crucial to take the steps below to protect your site from a politically motivated DDoS attack.
The Effects of a DDoS Attack
A DDoS attack might have a variety of effects, depending on the nature of the attack and how prepared you are for it.
1. Website Downtime
The most immediate and obvious effect is that your website is overwhelmed and becomes unavailable.
This means any business you gain via your website won’t be available to you until you get the site working again. It also impacts on your reputation as a website owner. And if you don’t fix the site quickly, it can affect your SEO as if Google crawls your site and finds it out of action, you will lose rank.
If your site is unavailable because of being overloaded, it will return a 502 bad gateway error, which will negatively impact your search rankings if you allow it to stay that way for too long.
I’ve also seen attacks where the site hasn’t been available for a number of days (because the owner didn’t know how to fix it and hadn’t kept a backup, more of which shortly), and when the site did go back online, all of the internal links in that site’s Google listing had been lost.
2. Server and Hosting Issues
If your site is subject to regular attacks that you don’t take steps to mitigate, this could lead to issues with your hosting provider.
A good hosting provider will give you tools to secure your site against DDoS attacks but if you don’t have this and you’re on shared hosting, the attacks may impact other sites on the same server.
3. Website Vulnerability
A DDoS attack could render your site more vulnerable to hacking as all of your systems are focused on getting the site back online, and security systems may have been put out of action by the attack.
Hackers might then find it easier to make their way onto your site via a back door once the DDoS attack has succeeded in paralyzing your site.
Follow-up attacks like this won’t always come from the same source as the requests that formed the DDoS attack: a clever hacker will know how to hide their tracks and use multiple IP addresses to attack your site, as well as how to hide their real location.
So if you are the victim of a DDoS attack, one of your first priorities should be ensuring your WordPress site is secure. This is arguably more important than getting your public-facing site up and running again, as another attack will only take you back to square one (or worse).
4. Lost Time and Money
Repairing a website that has been subject to a DDoS attack takes time. It can also take money.
If you don’t know what’s happened to your site and haven’t prepared for the possibility of an attack, you could end up having to rebuild your site from scratch (I’ve seen sites where this has happened). If you didn’t take a backup of your site, what are you going to restore it from? And if you don’t fix it quickly, the attack could have a long-term impact on your site’s SEO and business performance.
While the site is down, you could be losing money in revenue, especially if your site is an ecommerce store. And you may have to pay money to hire a security expert or web enveloper to rebuild your site and make sure it’s protected from future attacks.
All of this emphasizes how important it is to protect your site from DDoS attacks. I had one client who suffered frequent attempted attacks because of the nature of their business; because we set up security measures, these never impacted on the site. If you’re prepared, then a DDoS attack shouldn’t affect your site either.
What Can Make Your Website Vulnerable to DDoS Attacks?
Some sites are more vulnerable than others to DDoS attacks. These will either make you more vulnerable to the attack in the first place or to its after-effects.
Cheap Hosting
The first culprit when it comes to vulnerability to DDoS attacks, as with all kinds of cyberattacks, is cheap hosting.
Cheap hosting has two main downsides: lack of support and volume of clients.
To make it possible to offer the hosting so cheaply, the hosting provider will have a large number of clients all using the same server, meaning if one of the other sites on that server is subject to an attack, it could affect you.
Cheap hosting providers won’t provide security precautions against DDoS attacks, they won’t warn you when an attack takes place, and they won’t help you to repair your site when it stops working. They won’t take regular backups of your site and even if they do, they’re unlikely to help you restore your site: you’ll have to work out how to do it yourself.
This isn’t because cheap hosting providers are trying to con you or because they don’t provide the services they promise: it’s simply because to make their hosting cheap, they have to skimp on support. Otherwise, they wouldn’t make a profit.
If your website supports a business or any venture where your reputation and the security of your website is important, then it pays to invest in good quality hosting. The extra cost will be worth it when you avoid having to spend time fixing your site if it is attacked, and will certainly be worth it if it means your site stays online through an attempted DDoS attack and isn’t compromised.
Lack of Preparation
Failing to prepare for the possibility of a DDoS attack won’t necessarily prevent one happening, but it will mean you don’t suffer so much if you are subject to one.
Firstly, taking security precautions against potential attacks will enhance your site’s chances of staying online despite suffering an attempted attack.
But understanding how to stop a DDoS attack in its tracks will also help. If your site is attacked and does go down if you’ve prepared you will be able to get it up and running again much quicker than if you hadn’t prepared.
Installing security software or making use of the security alerts offered by your hosting provider means you will be alerted if your site does come under attack, and either you or your hosting provider can take action to protect your site.
Taking regular backups of your site means that you can quickly restore it if it does experience problems.
And keeping your site up to date means that it’s inherently more secure and will be less likely to encounter problems if you do have to rebuild it.
Insecure or Out of Date Code
Keeping your version of WordPress as well as your theme and plugins up to date won’t protect you from a DDoS attack.
But if you are attacked and the subsequent weakness of your site is used by hackers as an opportunity to gain unwanted access, they will be far less likely to succeed if your site is well managed.
Precautions include keeping your site up to date as well as only installing plugins and themes from reputable sources. The WordPress theme and plugin directories are by far the best places to find free themes and plugins, and reputable developers will make them available there. Be careful not to install code that might cause incompatibilities with your hosting and never install nulled themes or plugins.
How to Protect Your Site Against DDoS Attacks
So now for the question you’ve been itching to know the answer to: how do you protect your site against DDoS attacks?
There are a variety of precautions you can take, and which you choose will depend on your setup, your budget, and your preferences.
Let’s take a look at the options.
Protection from Your Hosting Provider
Kinsta hosting has a number of features that will reduce the chances of you being subject to DDoS attacks.
All of the sites hosted at Kinsta are protected by our Cloudflare integration, which features a secure firewall with built-in DDoS protection. We also make use of strict software-based restrictions to secure your site even further. All of this makes it much more difficult for a DDoS attack to get through.
Another Kinsta feature which can help protect you once a DDoS attack has begun is IP Geolocation blocking. Kinsta will detect any DDoS attack and alert you to it. You can then use the Geo IP blocking feature to block the geographical area from which the DDoS attack is coming.
This means you can safely block a geographical region where an attack is coming from and IP addresses from that region will no longer be able to send requests to your site.
Alternatively, you can block individual IPs in MyKinsta via the IP Deny page.
Here comes the hard truth, though: however good your hosting provider is, it’s impossible for them to provide total protection against DDoS attacks. What a good hosting provider will do is provide a good firewall, which will reduce the chance of an attack but not get rid of it altogether. They will also have tools you or they can use to stop the DDoS attack once it starts, such as IP blocking.
This is why any hosting provider that claims to give you total protection from DDoS attacks isn’t being entirely honest. They can reduce the probability of an attack and they can limit the impact of it, but they can’t stop DDoS attacks entirely.
Instead, to protect yourself from DDoS attacks more thoroughly you need to use a vast network that can use its database of information about attacks on other sites around the world to anticipate attacks and block IPs from which they re likely to come. Let’s look at a couple of those services.
Cloudflare
Cloudflare is one of the internet’s most popular providers of content delivery networks, and it also offers protection against attacks and hacks. Because of its vast size, it has access to information about where DDoS attacks are coming from and can then block those IP addresses for all the sites on its network.
Cloudflare’s cloud-based network is always on and always learning, meaning it can be identifying potential attacks and stopping unwanted traffic from reaching your site 24/7. It also provides you with a dashboard you can use to monitor and allay DDoS attacks so you can identify what your vulnerabilities might be.
If your site is hosted on Kinsta, you don’t need to go through the process of setting up your own Cloudflare account. All sites on our infrastructure are protected by our free Cloudflare integration.
Sucuri
Sucuri is a company best known for its services cleaning up sites after hacks and helping to prevent them from happening again. But it also offers DDoS protection

Sucuri’s service works because it is so large, with a network of over 400,000 customers meaning it can keep a database of attacks in the same way that Cloudflare can. Those IP addresses can then be blocked on your site.
Sucuri’s network isn’t as big as Cloudflare’s but the company is worth considering if you also want advanced security features and monitoring, which is where their specialty lies. Sucuri will monitor your site for downtime and attacks or hacks and will fix any hacks that take place.
So if you do suffer a DDoS attack and your WordPress site is hacked when it’s vulnerable, being with Sucuri means you can get it up and running again as quickly as possible.
Summary
DDoS attacks are becoming more common and they have the potential to cause billions of dollars worth of damage.
It’s impossible to completely protect yourself from DDoS attacks as there isn’t much control you have over the traffic coming to your site. But if you use one of the services above, avoid cheap hosting, and prepare yourself for a DDoS attack if one does occur, then you will be much less likely to suffer.


