OneLogin SAML SSO
OneLogin is an Identity Provider (IdP) that enables secure single sign-on (SSO), allowing your company’s users to access multiple applications with one login.
With Security Assertion Markup Language (SAML) SSO, employees sign in once using their company credentials (typically email and password). The IdP, such as OneLogin, verifies their identity and grants seamless, secure access to all connected services, without requiring separate logins for each application.
Company owners or IT administrators can link their organization’s email domain (e.g., @mycompany.com) to the IdP so that anyone with a company email address is automatically recognized and can securely sign in to SAML-enabled tools.
Using Kinsta SAML SSO, you can connect OneLogin to MyKinsta by creating a SAML application within OneLogin, verifying your company’s email domain, and adding the required OneLogin details in MyKinsta. This allows your team to log in with their existing company credentials, eliminating the need to create or manage separate MyKinsta accounts.
Enable SSO in MyKinsta
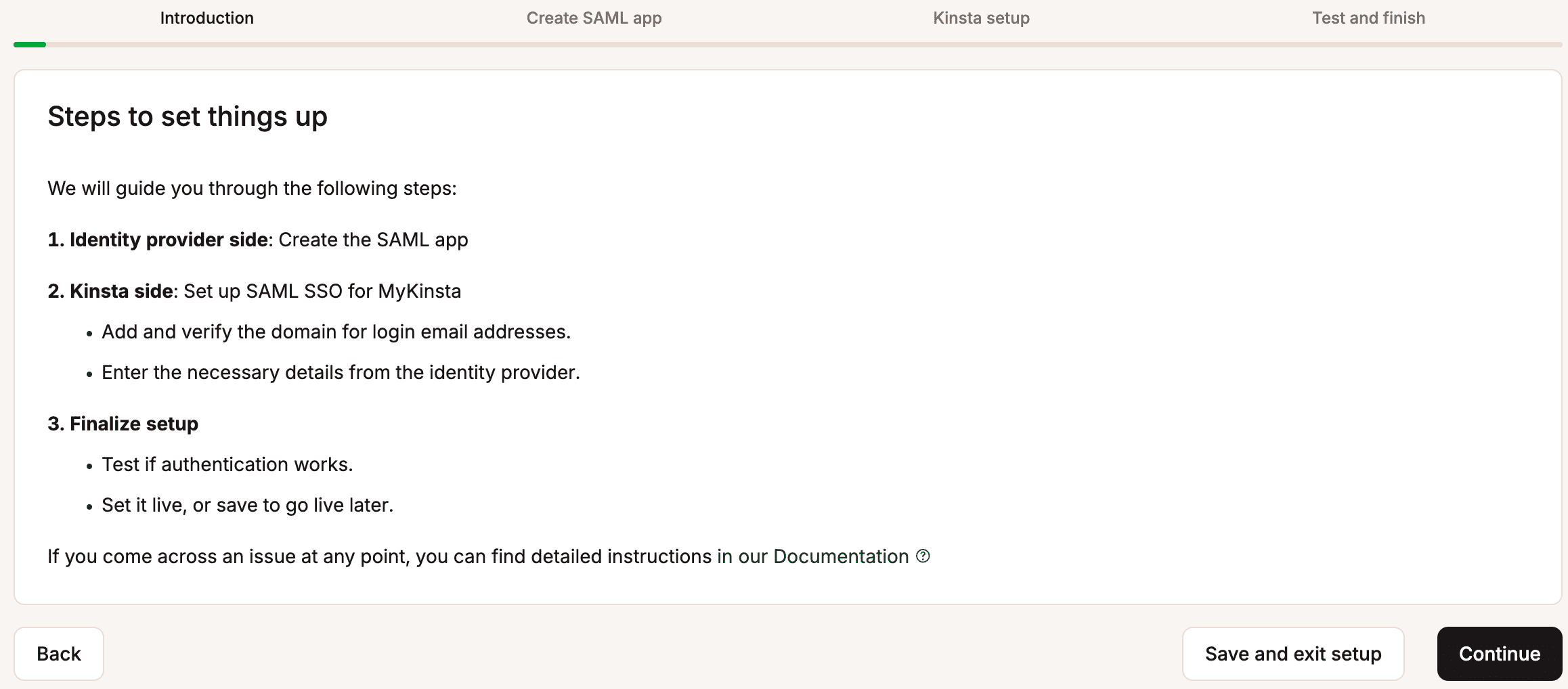
When you set up SAML SSO, you can click Save and exit setup at any stage to store your progress and return later.
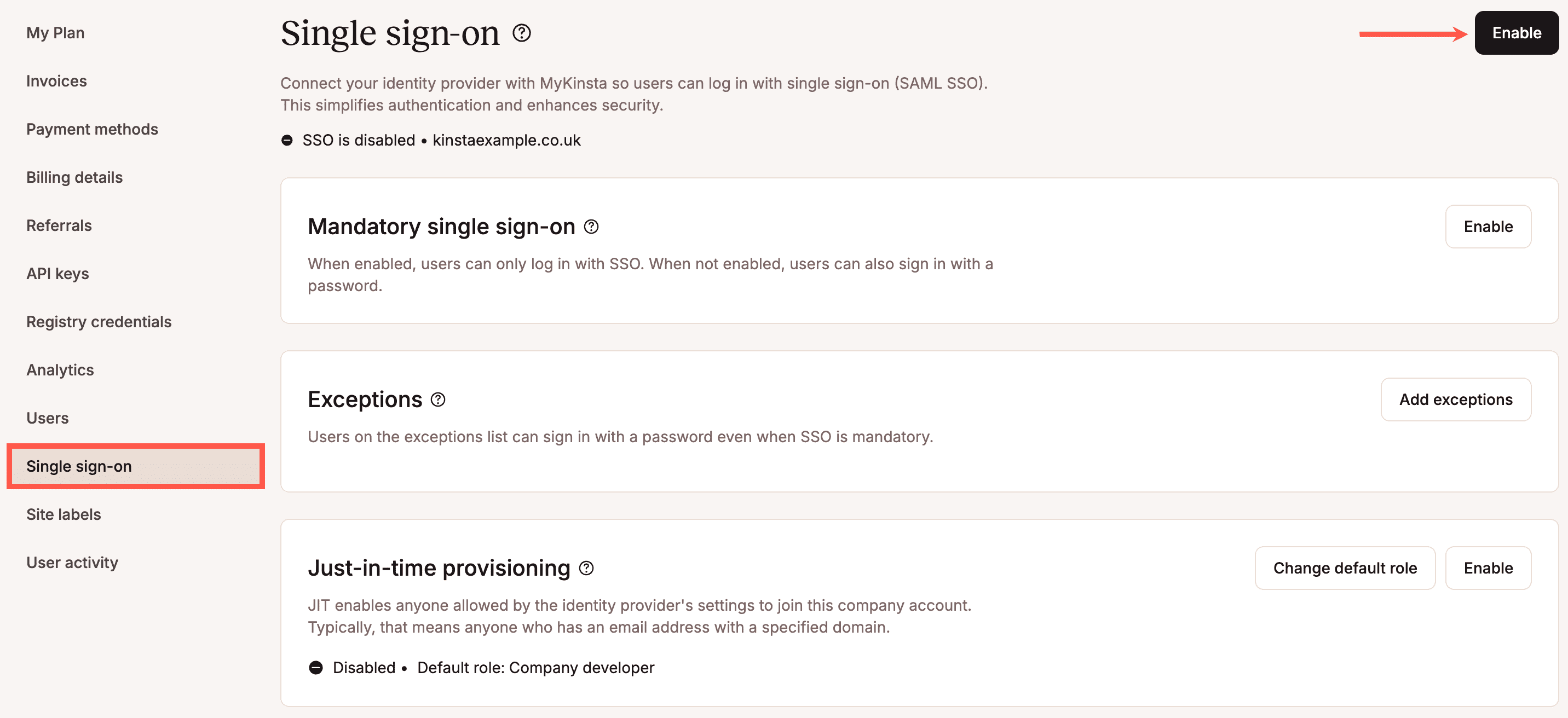
In MyKinsta, go to your username > Company settings > Single sign-on, and click Enable.
Read through the introduction, which explains how SSO will be set up, and click Continue.
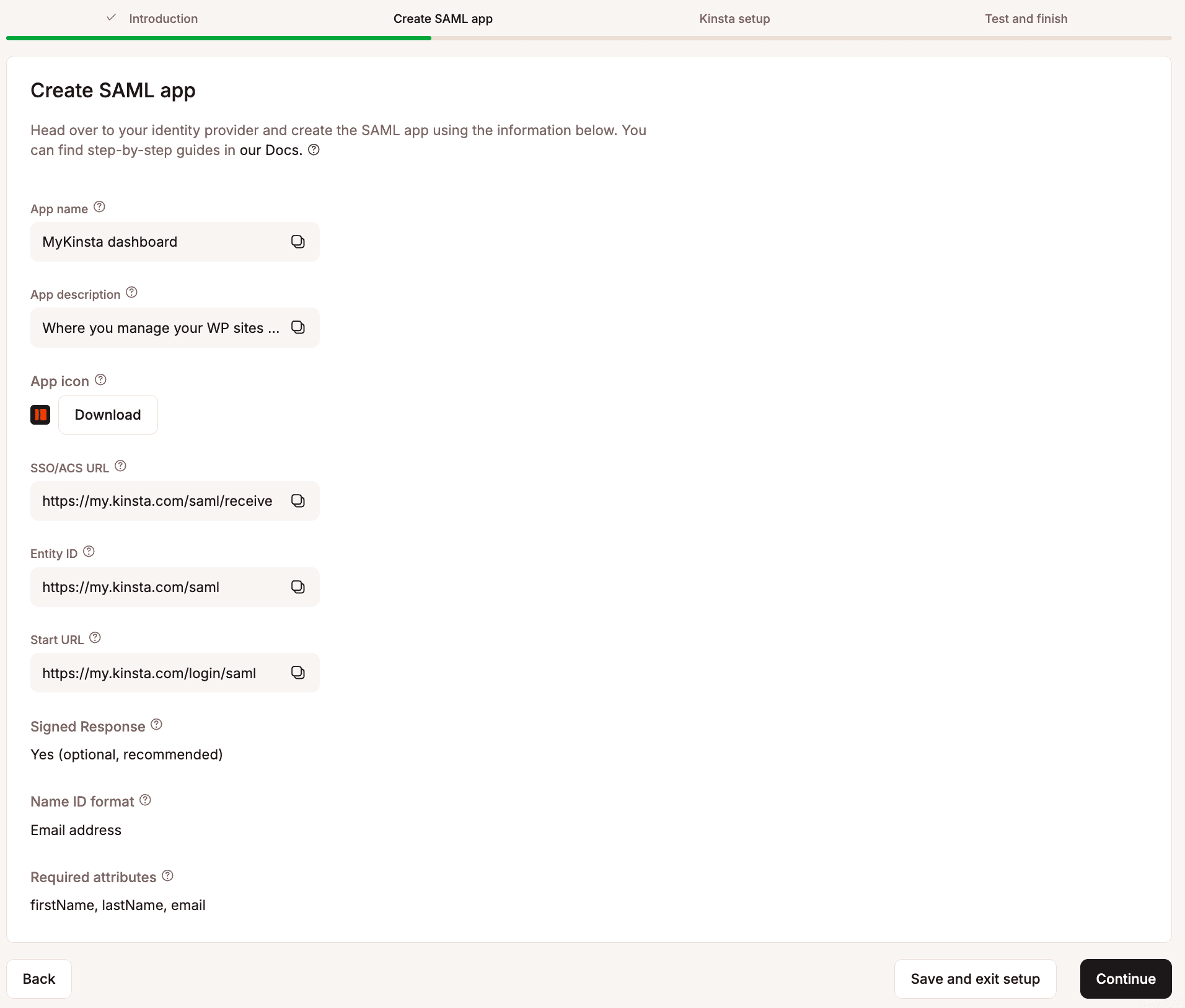
The next page provides all the information you need to set up your SAML app within OneLogin.
Set up the app integration in OneLogin
In MyKinsta, the Create SAML app tab provides all the information you need to set up your SAML app within OneLogin. The following steps explain where to add this information.
Log in to OneLogin as a user with admin access, and within Administration, click Applications > Applications > Add App.

Search for ‘saml custom connector’ and select SAML Custom Connector (Advanced).

In the Display Name, enter the App name from MyKinsta. You can also download the App icon from MyKinsta and upload this to the Square Icon, and add a Description if required. Click Save.

Click Configuration and complete as follows:
- Audience (EntityID): Copy and paste the Entity ID from MyKinsta.
- Recipient: Copy and paste the SSO/ACS URL from MyKinsta.
- ACS (Consumer) URL Validator: Copy and paste the SSO/ACS URL from MyKinsta.
- ACS (Consumer) URL: Copy and paste the SSO/ACS URL from MyKinsta.
- Login URL: Copy and paste the Start URL from MyKinsta.
- SAML initiator: Select Service Provider.
- SAML nameID format: Select Email.
- SAML issuer type: Select Specific.
- SAML signature element: Select Assertion.
- Sign SLO Response: Select this option.
- Sign SLO Request: Select this option.
Leave all other fields as default and click Save.

Click SSO, and within SAML Signature Algorithm select SHA-256, and click Save.

Map your OneLogin attributes
Within OneLogin, you must map the firstName, lastName, and email attributes from MyKinsta to the correct fields within OneLogin. For more information about how to do this, refer to the OneLogin documentation.
Assign users to the OneLogin app
In OneLogin, you can assign a policy to the application to allow all users using the policy to log in to the app. Go to Applications > Applications, select the application you set up for the MyKinsta Dashboard, click Access, choose the policy you want to assign, and click Save. For more information about security policies, refer to OneLogin’s documentation.
You can also assign individual users to the application. In OneLogin, click Users > Users, select the user you want to assign, click Applications, and click the plus icon.

From the Select application dropdown, select the MyKinsta application, and click Continue.

Select Allow the user to sign in, ensure the credentials are correct, and click Save.

To test authentication, make sure the MyKinsta user account you’re signed in with is assigned.
Kinsta setup
In MyKinsta, on Create SAML app, click Continue so that you are on the Kinsta setup page.
Email domain
In the Domain name, enter the email domain users will use to sign in using SAML SSO, and click Add domain.
Only MyKinsta accounts with an email address matching the verified domain can authenticate via SAML. For example, if SAML is enabled for example.com, only users with an @example.com email address will be able to sign in for that company.
If the domain has already been verified in MyKinsta through DNS management or as a site domain, it will automatically be verified. If it hasn’t, you’ll be prompted to add a TXT record to your DNS management service to confirm domain ownership.
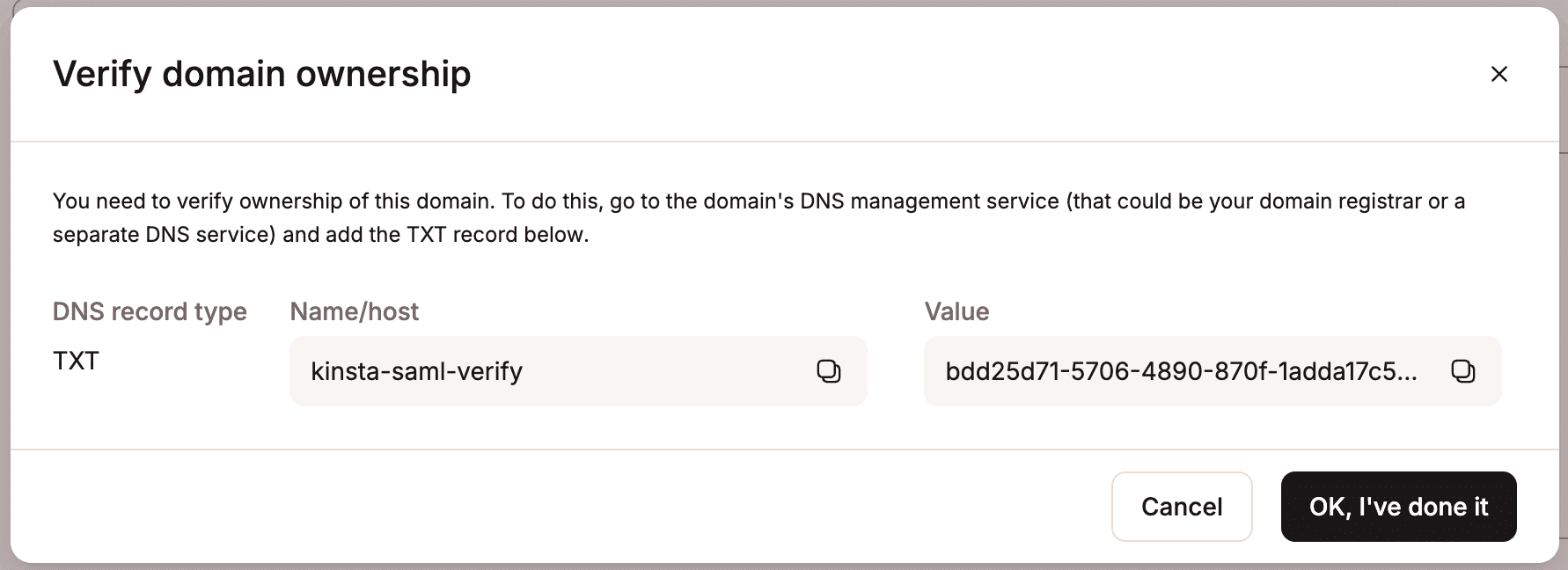
Because DNS changes can take time to propagate, you can click Save and exit setup to store your progress and return later.
Set up Kinsta SAML
In OneLogin, go to Applications > Applications, select the application you set up for the MyKinsta Dashboard, and click SSO.
This page provides all the information you need to set up SAML in MyKinsta.

In MyKinsta, within the Single sign-on Kinsta setup tab, complete the fields as follows:
- SSO URL: Copy and paste the SAML 2.0 Endpoint (HTTP) from OneLogin.
- Entity ID: Copy and paste the Issuer URL from OneLogin.
- Public certificate: In OneLogin, on the X.509 Certificate, click View Details, copy and paste the contents of the X.509 Certificate.
Click Continue.

Test the authentication in MyKinsta
You cannot enable SAML SSO within MyKinsta without first testing the authentication.
In MyKinsta, within the Single sign-on Test and finish tab, click Test authentication.
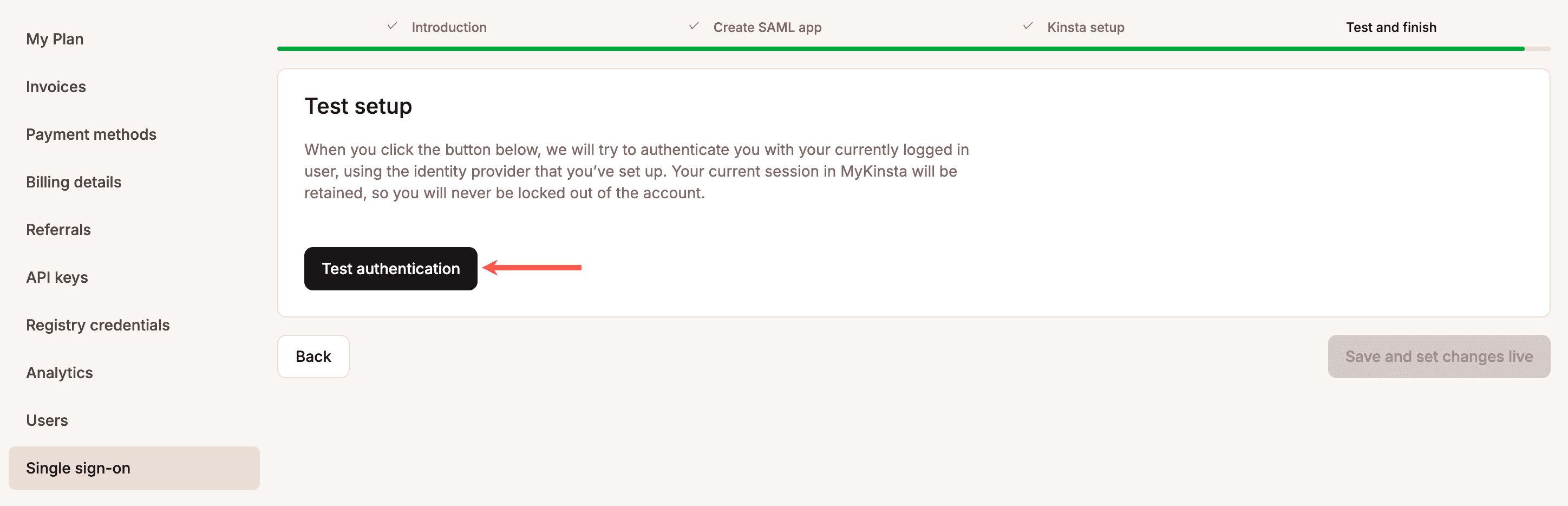
A notification appears if the test was successful or if the test fails.
If the test fails, click Back and check your SAML settings within OneLogin and within MyKinsta.
If the test is successful and you want to enable SAML, click Save and set changes live.
Your MyKinsta company users will now be able to sign in with SAML SSO or by entering their username and password. Users who sign in through an IdP are not required to complete Kinsta’s 2FA, as authentication is handled directly by the IdP.
If you want to force users to sign on via SAML, you can enable Mandatory SSO and add Exceptions. You can also enable JIT provisioning to allow users authorized by your IdP to access your MyKinsta company without requiring an invitation.

Change the session duration
Your Identity Provider (IdP) determines how long your SSO session remains active and when it expires. If your IdP doesn’t specify a session duration, MyKinsta defaults to a 24-hour session.
When your SSO session expires, you’ll be logged out of SSO. If you’re working within a company that uses SSO, you’ll be prompted to reauthenticate. If you have access to multiple companies in MyKinsta, you’ll remain logged in overall but will need to reauthenticate before accessing any company that requires SSO.
For details on adjusting session duration, refer to the OneLogin Knowledge Base.